Ahead of SEE 14, we examine how Internet technologies are evolving across South East Europe. Drawing on registry data and routing measurements, we highlight trends in routing security, interconnection, and IPv6 deployment.
The RIPE NCC South East Europe Meeting (SEE 14) takes place in Belgrade, Serbia, from 21-22 April 2026. The event will again bring together network operators, regulators, academics, and other stakeholders to exchange knowledge and explore the developments shaping the region’s Internet. The programme spans routing security and BGP behaviour, DNS, interconnection and IXPs, Internet measurements, and infrastructure developments.
As usual, to provide context for these discussions, we have prepared this report drawing on registration data, routing measurements, and deployment indicators to offer a clear, operational view of how Internet technologies are evolving across South East Europe.
Resources in the region
The figure below provides an overview of the distribution of Internet number resources across the SEE region as seen in the RIPE Registry. The overall picture has changed little since last year. Bulgaria still holds a clear lead in terms of members, while Romania remains ahead in terms of IP addresses (marginally with v6; significantly with v4). Beyond these larger allocations, we see plenty of variability in resource holdings.
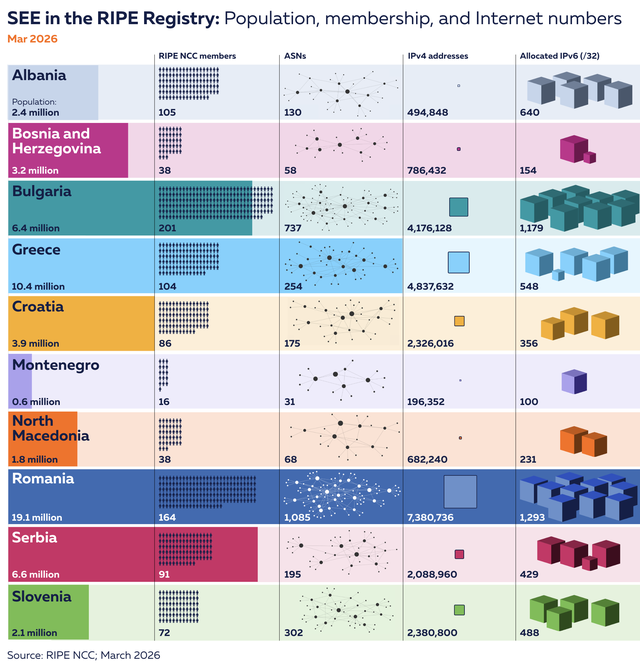
One thing to note is the relatively large ratio of members to population in Albania. This requires some explanation. The statistics in the image above are all derived from RIPE NCC registration data that uses 2-letter ISO-3166 codes as the unique identifier for countries. As explained in our 2023 article on Country Codes in the RIPE Database, these codes indicate in which country the resource holder is legally based.
However, in the SEE region things are more complicated due to Kosovo*. Because the world at large is divided over its status as a sovereign state, the ISO maintenance agency thus far has not assigned any code. Although some organisations have started using the unofficial "user assigned" code XK for Kosovo, this is not an option for the RIPE NCC - we can only use officially assigned code elements.
As an alternative we allow Kosovo members to register with the country code of their neighbours: RS (Serbia) or AL (Albania). A consequence of this is that our statistics for "AL" in fact cover both Albania and most of Kosovo. Unfortunately, that blurs the picture of the Internet in Albania.
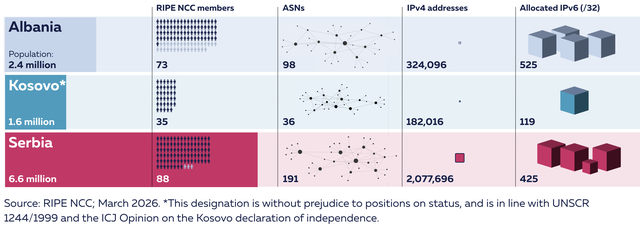
As the responsible RIR, however, we also know where members are incorporated. To assess the impact of the absence of an ISO code for Kosovo, we did an analysis in which we split members registered in RS and AL into three different groups, separating out those who have Kosovo as their legal address. The figure below shows how things stand after this adjustment. Compared to statistics based on country codes, we find that 37% of IPv4 addresses registered with Albania are in fact held by organisations whose legal address is in Kosovo.
Cybersecurity in the public sector
While the distribution of networks and IP addresses gives one view of a region’s Internet, we now turn to the operational challenges of running and securing them, chief among these being the need to detect and respond to cybersecurity incidents.
In its Global Cybersecurity Outlook 2026 report, published this January, the World Economic Forum noted acceleration of cybersecurity challenges "amid growing threats, geopolitical fragmentation and a widening technological divide", with AI "strengthening defence... while enabling more sophisticated attacks". Recent incidents in the SEE region have included attacks affecting public services and critical infrastructure, such as a ransomware attack in late 2025 that disrupted Romania’s water management systems and took around 1,000 computers offline.
An in-depth discussion of specific incidents is out of scope for this article. It is worth noting, however, that the majority (though not all) countries in the region have initiatives - e.g. CIRT and CSIRT teams - explicitly designed to respond to these threats. Here though, our goal is to look more specifically at how networks in the region are addressing security risks at the routing layer.
Routing security
Internet routing determines how data packets get forwarded across the Internet. The global infrastructure behind this relies on the Border Gateway Protocol (BGP), a protocol infamously designed with few if any inbuilt safeguards, leaving it prone to misconfigurations and hijacking events. In this section, we examine BGP incidents across SEE over the past year against uptake of RPKI.
RPKI allows IP address holders to publish Route Origin Authorisations (ROAs) specifying authorised origin ASes. Using Route Origin Validation (ROV), networks check BGP announcements against these ROAs to reject unauthorised origins and mitigate prefix hijacks and certain misconfigurations. ASPA is a new kind of RPKI signed object that adds another layer of protection (read more on this on RIPE Labs).
The chart below shows the number of BGP route origin incidents in SEE over the past year as seen by the Global Routing Intelligence Platform (GRIP).1 Each incident is counted once per country, using GRIP’s unique event ID together with the set of ASNs involved (both originating and covered / affected).
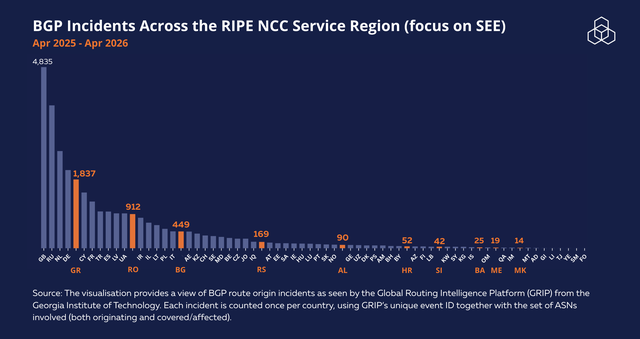
As we see, the SEE countries are quite evenly spread out across the plot. Even when the numbers are relatively low, BGP incidents have the potential to disrupt connectivity, misdirect traffic, and undermine the reliability of a country’s Internet. This is why making good decisions around routing security now is so important for future routing security.
ROA coverage
While there hasn’t been a big overall change in ROA coverage across the region over the past year, we do see a 9% increase for IPv4 address space in Bosnia and Herzegovina. In terms of IPv6, Croatia’s ROA coverage increased by about 8% since our last report.
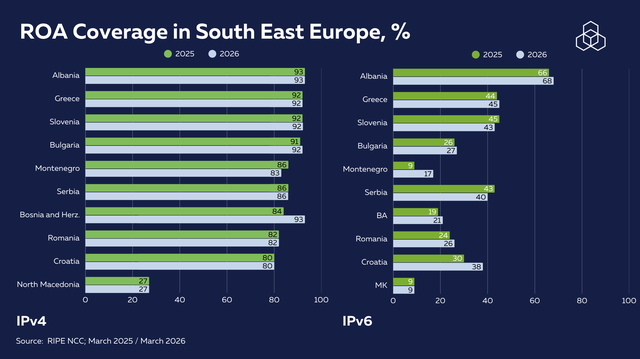
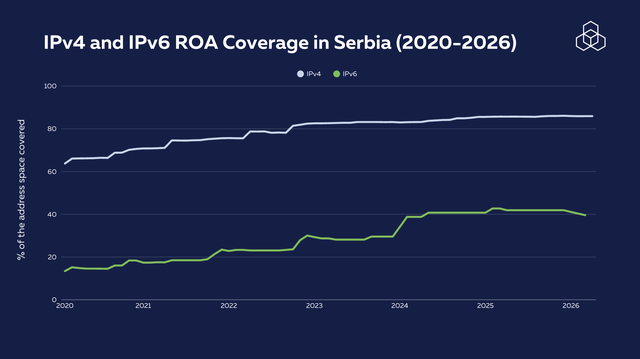
Serbia, the host of SEE 14, has seen a steady growth in ROA coverage, with nearly 90% of the IPv4 space and 40% of the IPv6 space covered with ROAs.
Protecting Internet infrastructure for government domains
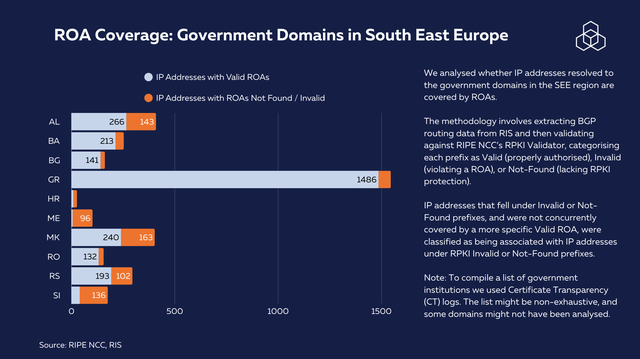
Government and public service domains form an essential part of the national digital infrastructure, supporting critical services such as healthcare, education, and public administration. For this same reason, the infrastructure behind these domains has been a common target for cyberattacks in different parts of the region in recent years. With this in mind, we analysed whether IP addresses for government domains in the SEE region are covered by ROAs (if you’re curious about our methodology, see note 2 at the end of the article).
Overall, the results point to varying levels of ROA adoption in government domains in the analysed countries. Greece stands out with by far the highest number of IP addresses covered by valid ROAs (1,486), indicating strong adoption of RPKI. In contrast, several countries, including Croatia, Montenegro, Slovenia and North Macedonia, display substantial gaps, with large numbers of IP addresses falling into the ROA Not Found or Invalid categories, suggesting incomplete or inconsistent implementation. Meanwhile, Bosnia and Herzegovina, Bulgaria, and Romania show relatively wider coverage, though still not comprehensive. Overall, the results highlight uneven RPKI adoption across the region, with clear leaders but also several countries where government domain routing security could be significantly improved.
ROV: From authorisation to validation
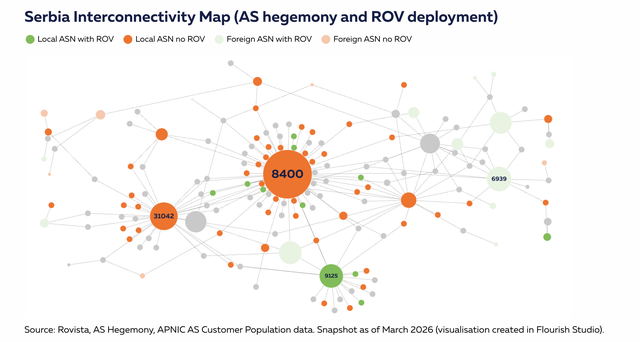
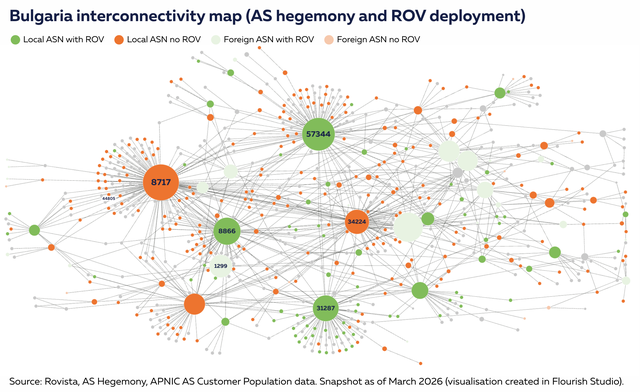
To analyse the deployment and impact of ROV in the region, we combined data from RoVISTA with a view of network centrality derived from AS Hegemony methodology, an approach that gives us a measure of the centrality of autonomous systems within a country. ROV deployment is inferred from routing observations: if RPKI-invalid routes are not seen propagating via a network, this indicates that the network itself, or one of its upstream providers, is filtering them. Conversely, if an invalid route successfully propagates to a network, it indicates that neither the network itself nor its upstreams along that specific path are dropping invalids.
Looking at Serbia first, we don’t see big changes in the deployment of ROV since last March. That said, Telekom Srbija (AS8400) - one of the largest telecommunications operators in South East Europe - is not yet dropping RPKI Invalids. Given this network’s centrality in Serbia’s interconnection landscape (indicated by its size in the plot), deployment here would be an opportunity to significantly improve the country’s overall routing security by deploying ROV.
There has been a positive improvement in Bulgaria’s network ROV deployment since the last SEE meeting that took place in Sofia. Telehouse (AS57344), a major colocation and transit network in Bulgaria, started to deploy ROV (or filtering is occurring at their upstream), thus enhancing routing security for the country's network landscape.
In Albania, we also see positive change, with One Albania (AS42313) having deployed ROV at the start of this year. As noted earlier, it should be kept in mind that some of the ASNs in the plot (those circled) are registered AL but belong to organisations whose legal address is in Kosovo.
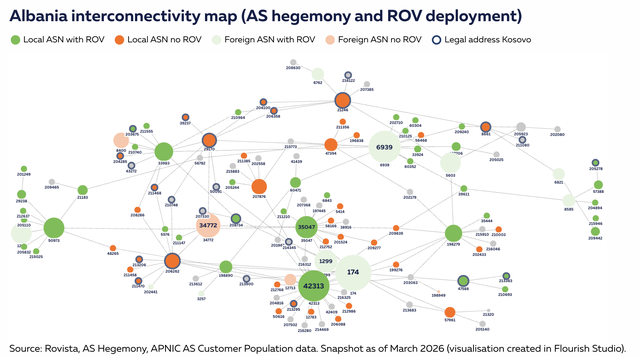
The interactive visualisation below gives a more complete picture of ROV deployment status across the region:
ASPA: A new layer of routing security
Autonomous System Provider Authorisation (ASPA) is a relatively new addition to RPKI that helps address routing incidents by enabling validation of AS path relationships. Still in its early stages of deployment, ASPA represents an important step towards strengthening routing security. As reported here on RIPE Labs last December, operators can create and manage ASPA objects alongside ROAs in the RIPE NCC’s RPKI Dashboard.
Since adoption is still emerging, this is the first time we've been able to include ASPA uptake figures in one of our regional reports. Across the RIPE NCC service region, around 2.93% of ASNs have published ASPA objects. Across SEE, uptake varies so far. Greece (7.84%) and Albania (6.92%) are notably ahead of the regional average, followed by Bosnia and Herzegovina (3.45%). Slovenia (2.32%) and Romania (1.84%) are somewhat below the RIPE NCC average, while Serbia (1.03%), Bulgaria (0.81%), and Croatia (0.57%) lag still further. At the time of writing, we don't yet see adoption in Montenegro or North Macedonia.
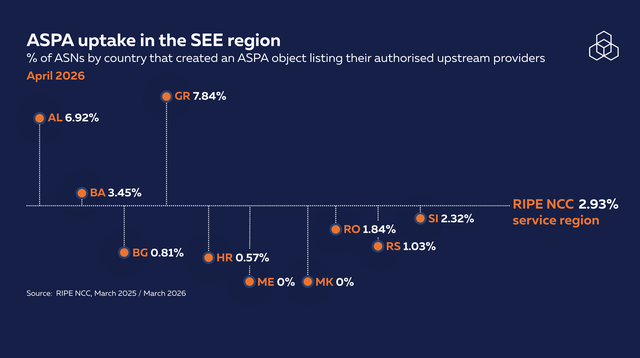
Looking at these figures, it's worth repeating that ASPA deployment is still in its early days, and even relatively small changes will significantly affect percentages going forward. Nevertheless, the variation across the region already highlights differing levels of engagement with this new routing security mechanism and suggests there is substantial room for growth in the coming years.
IPv6 Adoption in South East Europe
Now let’s turn to IPv6 adoption in the region. As we observed at the beginning of the report, IPv6 allocations are often proportional to the number of active Local Internet Registries (LIRs) registered for each country. Romania and Bulgaria still hold significantly higher amounts of active LIRs when compared to other countries in the region and lead by a wide margin when it comes to IPv6 allocations.
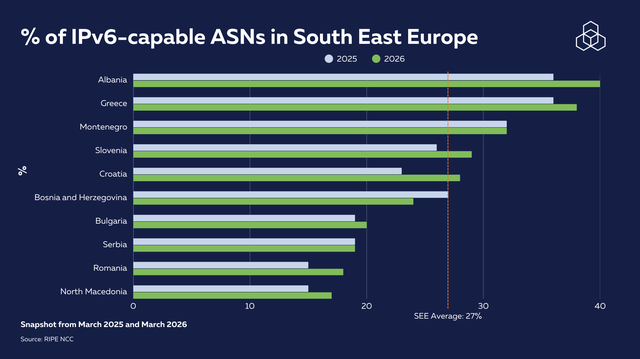
Given the vast size of the IPv6 address space, merely counting addresses would not provide a meaningful metric. Instead, we focus on the advertisement of prefixes by Autonomous Systems (ASes) as a key indicator of IPv6 capability.
In terms of IPv6 capability, defined as the percentage of ASNs routing at least one IPv6 prefix, Romania and Bulgaria show a lower percentage of IPv6-capable ASNs than some smaller countries in the region. This is partly a denominator effect: both countries have significantly more ASNs in total, meaning there is more room for networks yet to adopt IPv6. The absolute number of capable ASNs in both countries remains among the highest in the region. Since the last SEE report, IPv6 capability in Albania increased by 4%, to 40%.
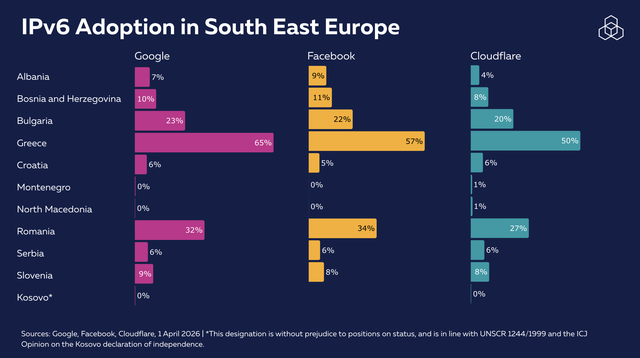
While IPv6 capability indicates the readiness of networks to use IPv6, actual adoption is not easy to measure. We looked at measurements reported by some major Content Delivery Networks (CDNs) on IPv6 adoption in the region. Recent data reveals varying levels of IPv6 adoption in South East Europe.
Google’s figures suggest particularly strong adoption in Greece (65%) and Romania (32%), followed by Bulgaria (23%), while several countries such as Montenegro, North Macedonia and Kosovo register 0%. Facebook and Cloudflare follow the same pattern for the region.
Differences in figures reflect the nature of CDN-based measurement: each platform observes only its own traffic, from its own user base, making cross-platform comparisons indicative rather than definitive. More fundamentally, IPv6 capability (whether a network announces IPv6 prefixes) and IPv6 adoption as seen by CDNs measure different things. A network can announce IPv6 prefixes without deploying them to end users, and CDN figures for smaller countries can be sensitive to which specific networks carry the platform's traffic. Taken together, the capability and CDN data offer complementary but partial views of where the region stands on IPv6.
Conclusion
In South East Europe, we see continued progress in the deployment of routing security measures and IPv6, alongside early adoption of newer approaches such as ASPA. While the pace and focus of deployment naturally vary between countries and networks, operators from across the region are engaging with the tools needed to strengthen the resilience of the Internet.
This report has focused on the routing layer as a key part of that resilience. Technologies like RPKI and ROV do not address all aspects of cybersecurity, but they are essential in reducing the risk and impact of routing incidents, helping to support a more stable and trustworthy Internet infrastructure.
As the community meets at SEE 14, these observations offer a shared point of reference for discussions on operational practices, deployment experience, and future priorities across the region.
Notes:
* For all references to Kosovo: this designation is without prejudice to positions on status, and is in line with UNSCR 1244/1999 and the ICJ Opinion on the Kosovo declaration of independence.
1. GRIP provides near-real-time observability of suspicious BGP routing events, including:
- MOAS (Multiple Origin AS), where the same prefix is announced by more than one AS
- Sub-MOAS, an event in which an AS announces a more specific prefix that lies within a covering prefix announced by another AS
Our analysis focuses on MOAS and Sub-MOAS events, as these can be mitigated by RPKI when invalid origins are detected, limiting their propagation in networks that enforce Route Origin Validation. To add geographic context, each ASN involved is annotated with its country of registration as recorded in the RIPE Database. We note that registration country does not necessarily reflect where an AS operates.
2. Our methodology involves extracting BGP routing data from RIS and then validating against RIPE NCC’s RPKI Validator, categorising each prefix as Valid (properly authorised), Invalid (violating a ROA), or Not-Found (lacking RPKI protection). We used Certificate Transparency (CT) logs to form a list of government institutions. The list might be non-exhaustive, and some domains might not have been analysed. IP addresses that fell under Invalid or Not-Found prefixes, and were not concurrently covered by a more specific Valid ROA, were classified as being associated with IP addresses under RPKI Invalid or Not-Found prefixes.







Comments 0