We wrote a user guide to help the community to understand the importance of deploying the BGP RPKI architecture and to give some practical guidelines to implement it in production networks.
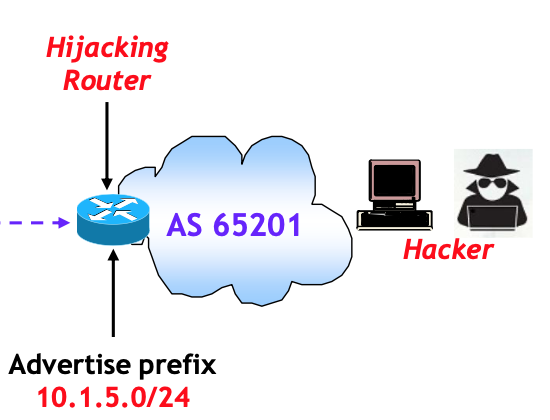
This includes a description of attack types, the theory behind Resource Private Key Infrastructure (RPKI) and practical configuration examples on Cisco and Juniper platforms.
For more information please download the full document: BGP RPKI: Instructions for Use




Comments 0
The comments section is closed for articles published more than a year ago. If you'd like to inform us of any issues, please contact us.