Following up from an earlier article on RIPE Labs, we now present 3 new Internet organizational layers to provide economic incentives to cooperate more on improving Internet security. What is needed is better coordination and motivation through reputational and financial incentives.
Introduction
| Figure 0: Financial and Political Layers |
|---|
At the recent Anti-Phishing Working Group (APWG) eCrime workshop in Dallas, a standing joke was that no paper was ever accepted anymore without "facebook" or "cloud" in the title. As businesses increasingly move sensitive data onto servers they don't own and whose locations they don't know, it's worth remembering that every cloud has a dark lining, in this case in the form of a thriving black market in spam, phishing, DDoS, and other criminal activity.
In our previous RIPE Labs article, we (the IIAR research project at the McCombs Business School of the University of Texas at Austin) talked about Economic Incentives for Cooperation to Fight Spam that can give Internet security a chance to catch up to the black market. Here's more detail about what we're proposing, in the form of Internet organizational layers.
Not technical protocol layers, as in the ISO layering model. Organizational layers, as in Evi Nemeth's old t-shirt (see Figure 0).
Existing Organizational Layers
The Internet already has a number of organizational layers.
What We Want
These are the layers we want, where users pay Email Service Providers (ESPs) for email (and other services) and get it, as in Figure 1 below (Note: You can click on the images to enlarge them. All the technical figures are also available in various sizes in a flickr set .)
Figure 1: Email Service Providers provide email to users
An ESP may be a traditional Internet Service Provider (ISP), or it may be a bank, a university, or any other organization that uses email on the Internet. The user may get email service as part of the deal for being a student or employee, or the user may pay. The important part is the user wants usable email, and many of the ESPs do: banks want to send statements and alerts; universities want students to correspond with professors; corporations want to update their customers.
What We Don't Want
Unfortunately, software isn't perfect, and often comes with vulnerabilities. Clever crackers write exploits for these vulnerabilities, and sell them to bot herders, who use them to take over computers, turning them into zombies or bots, building bot herds of thousands of compromised computers. Spammers buy access to these bots and use them to send unsolicited bulk email, or spam. A tiny percent of recipients pay for spam, fueling the black economy (see Figure 2 below).
Figure 2: Spammers buy access to botnets and use them to send spam
Botnets infest every kind of organization on the Internet that sends electronic mail. Spam: it's not just for ISPs anymore, any organization can be an electronic mail service provider (ESP) and any ESP can inadvertently send spam.
Software vendors release patches to deal with vulnerabilities, and a host of other IT security technical mechanisms (not pictured) have sprung up to deal with these problems, including anti-virus software, intrusion detection systems, patch distribution mechanisms, etc. These are all good and useful, but they have not solved the problem, partly because they are not used consistently enough. For example, there are huge numbers of computers still running outdated or unpatched software.
The Long But Slow Arm of the Law
The pre-existing layer of law enforcement organizations (LEOs) gets involved, due to new spam laws and old fraud laws. LEOs sometime arrest some of the miscreants and sometimes take down bots or bot herders' control computers (see Figure 3 below). (Other organizations also do takedowns; these figures are illustrative, not comprehensive.)
Figure 3: Law Enforcement Organizations can take down bots or bot herders' control computers
Unfortunately, the law is slow, funding is low, and takedowns usually don't last long: either somebody else takes over the botnet, or some other botnet takes its place.
Anti-Spam Blocklists
Meanwhile, technical people have constructed a higher layer of anti-spam blocklists, using spamtraps to intercept enough spam to tell where it's coming from, and then listing those spam source addresses so ESPs can use such blocklists to stop spam (see Figure 4 below).
Figure 4: Blocklists list spam sources so ESPs can filter those addresses
That's a big improvement, and more than 90% of email gets filtered out as spam before it reaches users, according to the ENISA 2009 Spam Survey. Still, many ESP and other resources are dedicated to doing that filtering and to routing and storing spam before it is filtered. The problem is not getting better, because ESPs generally go it alone.
Which organizations send the most spam?
At that eCrime workshop and before it at NANOG in Atlanta, I asked many people: "Which organizations send the most spam?" I don't mean spam gangs, as in Spamhaus' ROKSO registry of known professional spam operations. It would be nice if we could just track all of them down and have the LEOs arrest them, but that doesn't seem to happen very often. Meanwhile, which organizations are letting bot herders infest them and spammers use bots inside them to send spam out?
Nobody knew. Many could guess, but they were just guessing. And that would be very interesting to know, because nobody, not a bank, not an ISP, not a university, wants to be branded a spam haven.
They don't mean to, they don't know, and they don't want anybody to know. That's what Dilbert cartoonist Scot Adams calls a confusopoly. That's a market in which buyers can't even distinguish clearly on price because sellers keep important data hidden.
Fortunately, the data already exist to find out who lets spam out: it's in the blocklists. The biggest spamming organizations in the world are not who you might think as you can see in Table 1 below.
| Volume | ASN | CC | Description |
| 270597276 | 9829 | IN | BSNL-NIB National Internet Backbone |
| 165718151 | 24560 | IN | AIRTELBROADBAND-AS-AP Bharti Airtel Ltd. Telemedia Services |
| 147963786 | 7738 | BR | Telecomunicacoes da Bahia S.A. |
| 142822134 | 7643 | VN | VNPT-AS-VN Vietnam Posts and Telecommunications (VNPT) |
| 130337496 | 6849 | UA | UKRTELNET JSC UKRTELECOM |
| 110489232 | 27699 | BR | TELECOMUNICACOES DE SAO PAULO SA - TELESP |
| 103761533 | 9050 | RO | RTD ROMTELECOM S.A |
| 89794979 | 5384 | AE | EMIRATES-INTERNET Emirates Internet |
| 88841357 | 8167 | BR | TELESC - Telecomunicacoes de Santa Catarina SA |
| 84639370 | 25019 | SA | SAUDINETSTC-AS Autonomus System Number for SaudiNet |
| Table 1: Most Spam Volume Worldwide, 8 Sep 2010 - 7 Oct 2010. Volume (spam message counts) derived by the IIAR project from custom CBL blocklist data. |
There are several common features of these big spammers. Most are national or state telecommunications companies, so they have little competition. Many are in countries that are known to have a lot of pirated Windows software, where the users do not subscribe to patch updates, resulting in a lot of software that is both outdated and unpatched.
New Organizational Layers for Economic Incentive
The root of the ecrime problem is not technology: it is money. The black hats have a thriving black market that coordinates them and motivates them in hard cash. The white hats try to go it mostly organization by organization, and they're just a cost center. What is needed to beat the black hats is not new network protocols nor more laws: what is needed is better coordination and motivation through reputational and financial incentives.
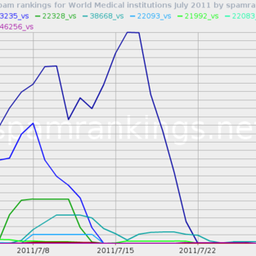
Rankings for Reputation in the Commons
The first step is to use blocklist data to distill rankings such as we just saw in Table 1, and to produce them comprehensively and regularly. Figure 5 (cropped from a larger figure that appears later in this article) shows a Reputation System Organization (RSO) doing this, and also producing drilldowns so organizations that rank as producing a lot of spam can get some clues as to why.
Figure 5: Reputation System Organization (RSO) distills rankings regularly
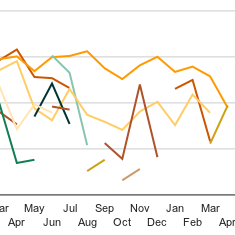
Rankings don't have to be perfect to be useful. They do need to be comprehensive, detailed, and frequent. For example, the organizations that emit the most spam in the ARIN region (U.S., Canada, and parts of the Caribbean) include AT&T, Comcast, Time-Warner (Road Runner), and Verizon, but in what order? Figure 5a includes all of them (and some others), but even if you guessed the order right for one day, you can see the order changes from time to time.
Figure 5a: Most Spam Volume in the ARIN region, 8 Sep 2010 - 7 Oct 2010.
Volume (spam message counts) derived by the IIAR project from custom CBL blocklist data.
Nobody wants to be known as the spammiest.
| Figure 5b: Elinor Ostrom, Nobel Prize, 2009 for her work on Governance of the Commons |
|---|
Reason to believe this approach will work is provided by Elinor Ostrom 's work on governance of the commons, which won the Nobel Prize in Economics in 2009 (see Figure 5b).
A commons is a common resource to which many people have access, as in a village common in Europe. There is fear that a commons may become overgrazed, because each villager has personal incentive to graze more sheep or cows and get more milk. If everyone does that, the commons becomes overgrazed, and is useless to anyone. In a great deal of discussion of this problem in the past forty years, the usual solutions proposed have been either to have the government control the commons, or to chop it up into pieces for each villager. Unfortunately, for government control to work, the government must have substantial current knowledge of the commons and how it is being used. Equally unfortunately, privatization often ends up with one entity buying up all the land and forming a monopoly, excluding or price-gouging the rest of the villagers.
Ostrom and colleagues examined many historical and present cases of commons, and discovered that there are other ways. After all, village commons existed in Europe for centuries, because the villagers could all see who was grazing how many sheep, and would have a word with whoever seemed to be overgrazing. And given that kind of transparency, the key feature is "management by the users themselves," as Robert Axelrod put it.
The reliability and security of the Internet, however, is a public good that cannot be ignored. The security of the Internet is a public good because availability to one user does not diminish its availability to another user.
...in large and complex systems, there should be multiple layers of nested enterprises (p. 101 f ). In the case of the Internet, individual users operate at a low level, while organizations and user communities operate at a middle level.
Transparency can enable “rewards for those with a good reputation in the public goods game,” ( Milinksi, et al., "Reputation helps solve the 'tragedy of the commons'", Nature 415, 424-426, 24 January 2002).
There is a place in all this for the law: to deal with actual criminals such as spammers and bot herders when caught. But nobody wants to lock up every person or company whose computers are infested by bots, even if it is because of negligence. The law may get involved in that as a last resort, but mostly other measures can be more effective and far more comprehensive. With reputation, existing Internet technical measures can be more widely and consistently employed, and we can even find out which ones work most effectively.
Certificates for Good Behavior
Rankings can be used by a Certification Authority (CA) to determine which organizations group together in which categories and then to issue certificates analogous to bond ratings, as in Figure 6 below.
Figure 6: Certification Authorities issue certificates based on rankings
A Certification Authority distills multiple RSO rankings over time to certify an ESP in a certain category. An ESP buys a certificate and uses it in marketing, just like a bond rating, or like a Good Housekeeping or Underwriting Laboratories seal of approval for successful spam prevention. ESPs already advertise certificates for specific security technologies. This CA certificate will go beyond that, to success of security technologies and procedures. The RSO and the CA thus enable a reputation system, floodlighting the formerly dark clouds of the Internet.
Blaming bad work is no more important than recognizing good work. It's important that this is not just about naming and shaming. It's also about bragging and praising: incentives.
Neither the RSO nor the CA is a governing body; neither tells anyone what to do, and neither has any enforcement power. Rather, each provides information and incentive for the stakeholders to organize themselves to collectively manage the Internet commons, (Thomas Dietz, Elinor Ostrom, and Paul C. Stern. "The struggle to govern the commons." Science , 302(1907), 2003.)
SLAs as Self-Insurance
Service Level Agreements (SLAs) say an ESP will provide service to its users within certain thresholds or pay penalties. An ESP can use rankings and certificates as external validation to turn an SLA into self-insurance to sell to its customers, as in Figure 7.
Figure 7: SLAs as Self-Insurance
A non-customer may want to sign up with an ESP that provides self-insurance SLAs, which thus enhance the ESP's reputation.
Insurance Against Moral Hazard
Traditional insurers can use rankings in writing and pricing insurance policies for ESPs, or they may buy self-insurance SLAs from ESPs as a form of reinsurance; see Figure 8.
Figure 8: Insurance Against Moral Hazard
To reduce moral hazard, an insurer may impose requirements on ESPs and their users. Just as a fire insurance policy often requires a sprinkler system, an anti-spam and anti-botnet insurance policy may require use of blocklists for both inbound and outbound spam, and perhaps even effective botnet takedown procedures. Such an insurance policy may also require a certificate from the CA, and the level of that certificate could strongly affect the price of the policy: insurance with an Aa certificate would cost a lot less than with a Bbb certificate. ESPs with such policies will advertise them, along with their certificates and security measures. Insurance will thus shine a gold light on an ESP's reputation.
Summary
By adding three new organizational layers (rankings and certificates for reputation, SLAs for self-insurance, and insurance against moral hazard), we can progressively build upon anti-spam blocklist data to produce organizational rankings and certificates for a reputation system, and then leverage those to turn SLAs into self-insurance, and to motivate insurance which will involve requirements on users and ESPs to reduce moral hazard (see Figure 9).
Figure 9: All new organizational layers combined
In Figure 9 we can see that insurance claims adjustment can draw on RSO drilldowns into the rankings to find out how well the ESP has really been doing. In addition, all of rankings, certificates, SLAs, and insurance provide reputation that customers and investors can use in selecting ESPs.
All of these new layers will promote cooperation among ESPs and users to provide better Internet security.
Incentives to Better Deploy Effective Security Measures
Since these layers will provide financial incentives for ESPs to prevent or stop spam, they will provide incentives to better deploy IT security measures, to find out which measures work best, to reward IT security personnel who implement measures that work. This could even result in IT security changing from a cost center to a profit center. It would also provide more business for IT security companies that sell products that effectively reduce spam and improve security.
Finally, Figure 10 shows all the old and new levels. Green is good, red is bad, sky-blue is for reputation, and gold is for financial incentives.
Figure 10: All old and new organizational layers combined
These layers can bring quantification and experimental rigor to a commons model of the Internet, while providing the reputational and economic motivation needed to organize IT security to defeat the spam and botnet black market.
The data are available. We know how. Let's try it.
Further articles, and feedback please
This is the first of a trilogy of RIPE Labs submissions:
- Internet Cloud Layers for Economic Incentives for Internet Security
- Calibration of rankings using multiple blocklists
- Internet social comparison theory experiments using rankings
We will be presenting a talk at RIPE 61 in Rome, 16 November 2010, tying all this material together.
We are interested in receiving feedback on this study from the RIPE community. What do you think about these proposed new organizational levels for economic incentives for cooperation for Internet security?
Acknowledgments
This material is based upon work supported by the National Science Foundation under Grant No. 0831338. Any opinions, findings, and conclusions or recommendations expressed in this material are those of the author(s) and do not necessarily reflect the views of the National Science Foundation.
We also gratefully acknowledge custom data from CBL, PSBL, Fletcher Mattox and the University of Texas Computer Science Department, Quarterman Creations, Gretchen Phillips and GP Enterprise, and especially Team Cymru. None of them are responsible for anything we do, either.
John S. Quarterman for the IIAR project, Andrew B. Whinston PI, Serpil Sayin, Eshwaran Vijaya Kumar, Jouni Reinikainen, Joni Ahlroth, and other previous personnel.
antispam@quarterman.com

Comments 5
The comments section is closed for articles published more than a year ago. If you'd like to inform us of any issues, please contact us.
Anonymous •
The points and issues raised in this article is bang on. We know the list of ISP's that are the major sources of spam. One thing that caught my eye was that most of these were state owned corporations such as BSNL (No.1). <br /><br />Take a look at this. <br /><br /><a href="http://mailchannels.com/product/" rel="nofollow">http://mailchannels.com/product/</a><br /><br />The MailChannels Outbound product is meant to do exactly the kind of outbound spam filtering for ESP's that is mentioned here. So why aren't products like these getting implemented by the ISP's? <br /><br />Creating an eco-system where products like these are installed at all the ISP's would help solve this big problem.<br /><br />Any thoughts?<br /><br />
Anonymous •
Yes, that's the idea.<br /><br />At the moment, few ESPs use such products because they view outbound<br />spam as an economic externality, as somebody else's problem.<br /><br />I don't know about the relative merits of this particular product,<br />but bringing visibility to which ESPs are doing well at stopping<br />outbound spam will give them all incentive to use products like that.<br />Also to get their users or employees to patch up to date, etc.<br /><br />-jsq
Anonymous •
<a href="http://labs.ripe.net/Members/jsq/economic-incentives-for-internet-security" rel="nofollow">http://labs.ripe.net/[…]/economic-incentives-for-internet-security</a><br /><br />misleading route<br />Network Data<br />Network id#:1<br /> <br /> Query terms are ambiguous. The query is assumed to be:<br /> n 192.168.1.1 <br /> <br /> Use ? to get help.<br /> <br /><br /><br />Network id#:2<br /> <br /> Query terms are ambiguous. The query is assumed to be:<br /> n 68.42.10.1 <br /> <br /> Use ? to get help.<br /> <br /><br /><br />Network id#:3<br /> <br /> Query terms are ambiguous. The query is assumed to be:<br /> n 68.87.214.21 <br /> <br /> Use ? to get help.<br /> <br /><br /><br />Network id#:4<br /> <br /> Query terms are ambiguous. The query is assumed to be:<br /> n 68.85.78.165 <br /> <br /><br />
Anonymous •
This definition (see above)<br /><br /> An ESP may be a traditional Internet Service Provider (ISP),<br /> or it may be a bank, a university, or any other organization<br /> that uses email on the Internet.<br /><br />may be misleading. I formerly used that term myself, but found out that for lots of people "ESP" means an organization that carries out email marketing on behalf of their customers. "Mailbox provider" is unambiguous. See <a href="http://www.ietf.org/mail-archive/web/marf/current/msg00517.html" rel="nofollow">http://www.ietf.org/[…]/msg00517.html</a>
Anonymous •
Good point, and noted for further presentations.