The second Coordinating Attack Response at Internet Scale workshop (CARIS2) met earlier this year to discuss changes to infrastructure and monitoring as on-the-wire or transport encryption becomes stronger (for example, TLS 1.3 and QUIC) and ubiquitous.
The overall theme for CARIS is to better scale incident response, which also includes research leading to attack prevention in protocols and systems. Security controls and incident detection techniques will inevitably shift to the endpoint, requiring innovation to better secure our networks and develop new detection capabilities.
There are numerous research areas to explore related to this shift and CARIS2 worked to prioritise viable concepts that emerged from collaborative brainstorming breakouts, some of which I’ve summarised below. You can learn more by reading the full report (in development).
Many hands (and minds) make for interesting work
CARIS2 drew a diverse set of participants, which aided productive collaboration. The workshop had four main breakout sessions, with specific objectives and guidance enabling brainstorming in non-competitive areas to ensure open collaboration and progress the workshop themes. The generated research ideas also facilitated a work stream to progress ideas, possibly through the IETF, or IRTF.
The presentations from selected papers served as an introduction to either a model to emulate for scaling, or for balancing defence and monitoring capabilities while considering privacy in an encrypted world.
In the first case, there are some strong examples such as the Manufacturer Usage Description (MUD) protocol where a “manufacturer” (which could be a vendor or even a distributor) establishes the expected use profile for a device. The MUD profile can be updated by the manufacturer when new firmware or software is released or in the event of a vulnerability announcement.
By shifting the responsibility of generating filters that can go beyond the access control level of ports and protocols to the manufacturer, the security management scales – in that a small number of analysts can set the policy for devices widely deployed in numerous environments. The Protocol for Automatic Security Configuration (PASC) and the Protocol for Automatic Vulnerability Assessment (PAVA), builds upon MUD and also holds promise for scaling security management.
The paper on IPv6 aggregation served as an excellent introduction to a brainstorming session determining methods for conducting monitoring while considering privacy. The IPv6 aggregation work was developed by two researchers, Dave Plonka and Arthur Berger, who perform measurement research with access to large amounts of data at Akamai. With an interest in using IPv6 data at the endpoint, but protecting user privacy in the middle of the network, this idea works to balance measurement capabilities with privacy for end users. Using this work as an example to promote similar methodologies for research on monitoring and measurement has the potential to overcome the ‘arms race’ between network monitoring and privacy in technology standards. See the CARIS2 report and papers for more information on projects resulting from this breakout discussion.
Another breakout that had participants quite engaged, examined the effectiveness of indicators or incident exchange groups, exploring opportunities to improve the efficiency and scale of response. This breakout followed a different format that kept participants actively engaged after two long days participation.
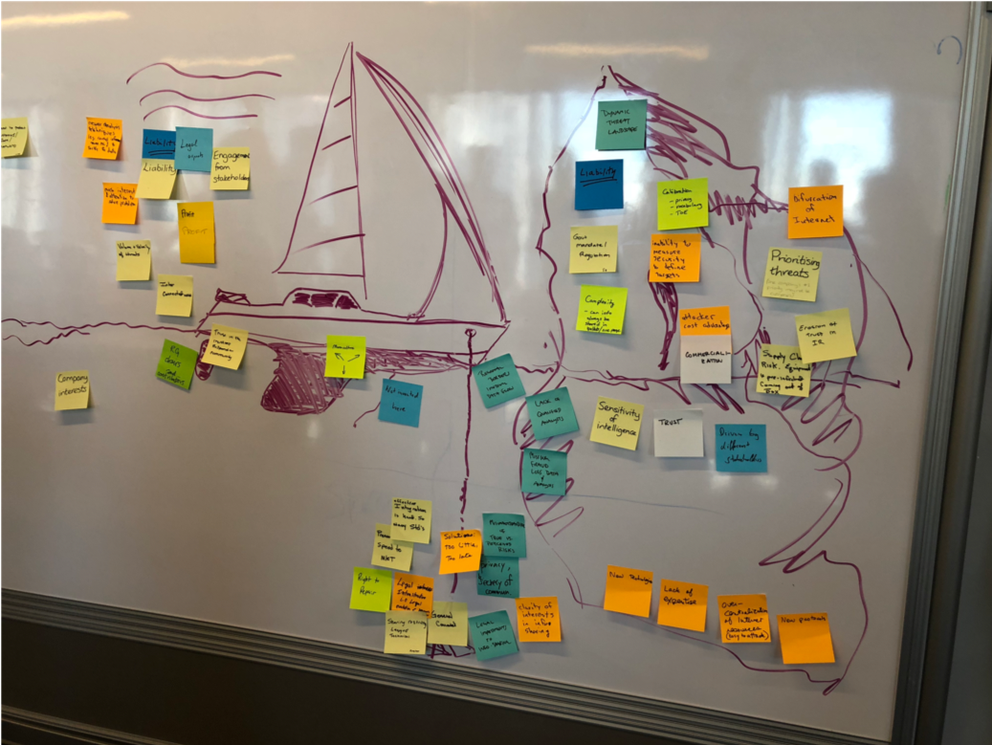
Figure 1: Whiteboard at an incident response breakout at CARIS2
An artist in the room drew a sailboat on the whiteboard with wind in its sails, an anchor, and an iceberg looming ahead. Each participant had sticky notes to write out what they felt was supporting incident responders (wind in their sails), holding them back (anchor), and what trouble lay ahead (iceberg). The resulting prioritised list provides rich research opportunities to advance incident response in terms of efficiency and scale. A few highlighted items include:
Supporting
- Trust in incident response teams
- Need to protect network as a forcing
function - Current efforts supported by profit
- FEAR – initially a burst of wind, but
eventually leads to complacency
Dragging
- Too many standards
- Regional border impact data flows
- Lack of resources/participation
- Monoculture
Looming problems ahead
- Dynamic threat landscape
- Liability
- Bifurcation of Internet
- Lack of skilled analysts
- Sensitivity of Intelligence/trust
The results are summarised in more detail in the report and will be useful in research to improve the problem space.
I’m encouraged by the output and work efforts resulting from CARIS2 and look forward to resulting research work and future CARIS workshops.




Comments 0
The comments section is closed for articles published more than a year ago. If you'd like to inform us of any issues, please contact us.