Following up on our series of regional reports, we present developments in routing security and IPv6 uptake in South East Europe (SEE). We look into the changes in RPKI deployment and IPv6 capability for networks in the region ahead of the upcoming SEE 13 meeting that will take place in Sofia, Bulgaria.
The primary goal of this article is to trace developments that have taken place in routing security and IPv6 uptake in the SEE region since our 2024 report. At the same time, as we work through the numbers and data, we also hope that this report will help prompt positive decision making by illustrating the real benefits that come with the uptake of the key Internet technologies and identifying specific areas where meaningful progress can still be made.
SEE at a glance
As of the most recent DESI 2022 report, issued in 2022, the SEE region was shown to be positioned just slightly behind the EU as a whole in terms of digital performance. As indicated in our last report though, ambitions for digital transformation continue to drive progress in the development of technical infrastructure, if at somewhat different rates across the region. Montenegro leads in terms of broadband connectivity, followed by Serbia, Kosovo, and Albania, with progress often tied to the initiatives of large telecom operators like Telecom Serbia and Hrvatski Telekom. These providers, who control much of the region’s address space, are pivotal in advancing Internet technologies, such as for example, RPKI and IPv6.
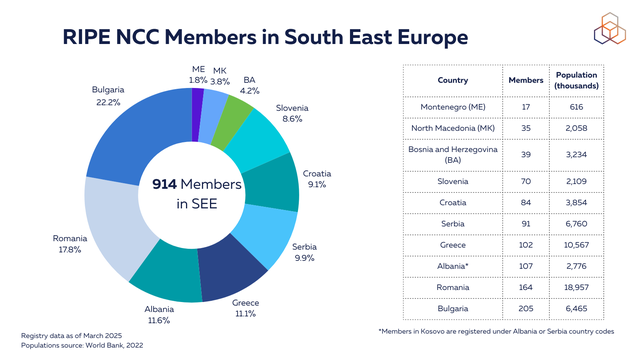
RIPE NCC membership distribution in the region hasn’t significantly changed since the last SEE meeting. Despite the country's relatively small population size, members registered in Bulgaria make up 22% of the RIPE NCC membership among the countries in the region.
Cybersecurity in the public sector
According to a recent report from the Balkan Investigative Reporting Network (BIRN), cyberattacks in the Western Balkans surged after the start of the war in Ukraine in 2022 due to heightened geopolitical tensions and a related increase in both state-sponsored and criminal cyber operations. Many of these attacks targeted government and critical infrastructure systems - e.g. e-services for energy, healthcare, education, etc.
In March 2022, a cyberattack on the Independent Media Commission (a key regulatory body in Kosovo) resulted in the loss of critical data and significant disruption of operations. In July 2022, a "highly destructive cyberattack" was launched against e-Albania. In August, the government website for public services in North Macedonia was brought down, followed by the website of the Ministry for Education and Science one month later. At around the same time, Montenegro was encountering a prolonged cyberattack "described as the most significant in its history", which targeted key government institutions, including courts and the Revenue and Customs Administration. Similar incidents were also reported in Serbia, Bosnia and Herzegovina, and Turkey.
The BIRN report states that, as digitalisation of government systems has continued to advance across the region, the vulnerability of these systems to such attacks has become increasingly apparent. It also notes that while the Western Balkans has made considerable progress in strengthening cybersecurity frameworks, they have mainly been driven by external factors such as EU directives, suggesting room for more local initiatives.
These incidents highlight the current position of government organisations in the cybersecurity ecosystem and the clear need for closer attention to security measures. While discussion of countermeasures against cyberattacks is not in the scope of this article, we can provide a better view of routing security in the SEE region.
Routing security - Shielding Internet paths
The global Internet’s routing infrastructure still depends on the Border Gateway Protocol (BGP), a system originally built on mutual trust between networks. As the Internet has grown more complex and interconnected, this trust-based model requires additional safeguards - particularly in regions like South East Europe, where networks often play a role in regional transit. The Resource Public Key Infrastructure (RPKI) helps address this need by enabling cryptographic verification of route origins.
RPKI provides a framework for verifying BGP announcements using two main components:
- Route Origin Authorisation (ROA): A digitally signed object that specifies which Autonomous System (AS) is authorised to announce a given IP prefix.
- Route Origin Validation (ROV): The process of checking incoming BGP announcements against published ROAs. Routes are classified as Valid, Invalid, or Not Found, and Invalid routes can be rejected by routers.
Before examining deployment levels, we analysed BGP route origin incidents in South East Europe and neighbouring countries using Cloudflare’s BGP incident data. Each incident is counted once per country, regardless of whether the country was the origin or a victim. We define an incident by a unique combination of the incident ID and the Autonomous System Numbers (ASNs) involved, both the originating and affected parties.
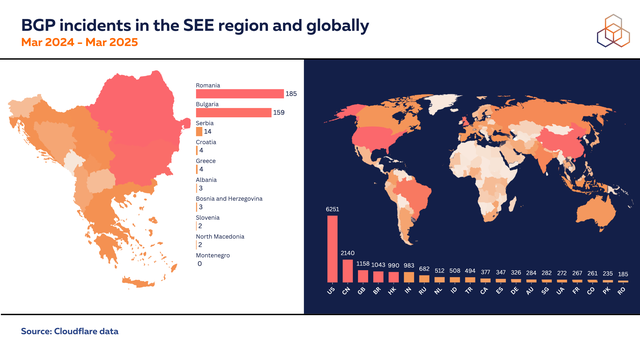
Romania and Bulgaria show higher numbers of routing anomalies than other countries in the region. Both have a significantly larger number of registered IP prefixes and ASNs. This greater volume of routing resources likely results in more BGP activity and, consequently, more opportunities for routing anomalies to occur. While we do not draw conclusions about the cause or intent behind these incidents, the correlation with routing scale is clear.
However, the number of incidents alone does not capture the full picture. A single BGP hijack can have serious consequences, especially when it involves government networks or critical infrastructure such as ISP or DNS service prefixes. These events can disrupt connectivity and essential services across large areas. That’s why route security measures like RPKI are important for all networks – regardless of how many incidents they’ve experienced. A consistent, system-wide approach to route origin validation is essential for improving overall routing resilience.
Historical examples highlight what’s at stake. In 2008, an accidental route hijack by Pakistan Telecom disrupted global access to YouTube, showing the dangers of unauthenticated announcements. More recently, Iraq’s 2023 attempt to block Telegram had less impact in networks where ROV was in place. These cases illustrate how route origin filtering can reduce the spread and impact of invalid announcements. In South East Europe, RPKI adoption remains inconsistent, leaving many networks potentially exposed to similar risks.
To implement RPKI effectively, network operators must take two main actions: publish ROAs for all IP prefixes through their Regional Internet Registry (RIR), and configure ROV on their routers to filter out invalid BGP announcements. ROAs should cover all actively routed prefixes, including aggregates and any more specific subnets that are advertised. Operators should ensure that ROAs accurately reflect what is announced in BGP to avoid creating unnecessary exposure. For address space that is not intended to be routed on the public Internet, ROAs with origin AS 0 can be used to indicate that no origin is authorised.
Improving routing security in South East Europe is a shared responsibility. Network operators play the central role, but governments and industry bodies can support progress through policy, training, and outreach. As digital infrastructure in the region continues to expand, consistent implementation of route security measures like RPKI will be essential to maintaining stability and trust in the global routing system.
RPKI Deployment in South East Europe
For more on RPKI and details on how ROA and ROV coverage are measured, see this article from last year.
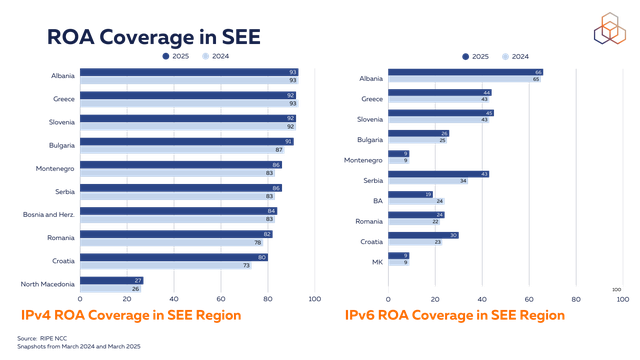
Across South East Europe, ROA coverage is generally high. For IPv4, most countries in the region show coverage between 80% and 90%, with the exception of North Macedonia, which remains significantly lower. IPv6 coverage is more variable, ranging from around 10% to over 60%. Albania and Greece lead in ROA deployment for IPv6, with a consistent upward trend.
It is important to note that networks in Kosovo are typically registered under the Albania country code (AL) in the RIPE Database, while some are registered under the Serbian country code (RS). This is reflected in all data analysed for this article. As a result, certain networks - e.g., IPKO Telecommunication (AS21246), Telekomi i Kosoves (AS8661), Artmotion (AS33983), Kujtesa Net (AS29170), all of whom have ROAs in place for their address space - belong to the companies operating from Kosovo.
Country codes for ASNs assigned by the RIPE NCC are drawn from the current list of assigned ISO 2 codes and are based on where the AS holder is incorporated. While this gives us one way of thinking about about the geographical locations of ASes, ASes themselves are not bound to specific countries.
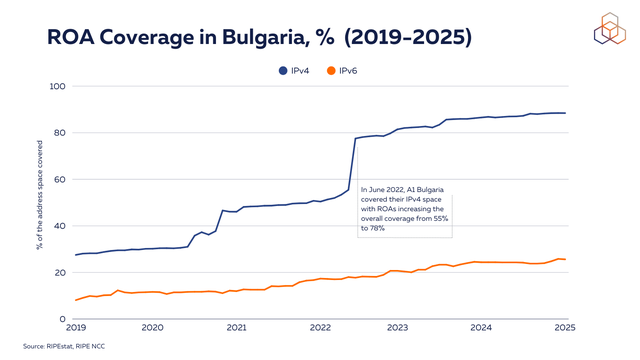
Zooming in on Bulgaria, the country shows high ROA coverage for IPv4. It saw a steady increase with a considerable jump from 55% to 78% in June 2022, when A1 Bulgaria covered their IPv4 space with ROAs. IPv6 coverage is growing gradually but remains low, currently just above 20%.
Securing government domains with ROA
Governments and regulators often act as catalysts for the adoption of IPv6 and RPKI. As RIR for Europe, the Middle East, and parts of Central Asia, the RIPE NCC actively engages with these actors, and we recognise that their support is crucial to driving technological advancements. Such collaboration has already yielded tangible results. For example, engagement with governmental authorities in Saudi Arabia has contributed to significant progress in RPKI adoption there, while similar efforts in the United Arab Emirates have helped accelerate IPv6 deployment.
Government and public service domains form an essential part of national digital infrastructure, supporting critical services such as healthcare, education, and public administration. As discussed earlier, these domains are not only highly visible, but also increasingly targeted by cyberattacks. Without ROAs in place, the IP address space associated with these domains is more vulnerable to routing incidents, including BGP hijacks and accidental misconfigurations.
To assess the extent of this exposure, we conducted a preliminary analysis of ROA coverage for IP addresses linked to government and public service domains in some of the SEE countries such as Albania, Bulgaria, Montenegro, North Macedonia, and Serbia. While the dataset is not exhaustive, the findings offer valuable insights into the current state of RPKI deployment in the region.
The methodology combined DNS resolution and routing validation. A set of government-related domains was assembled from publicly available sources. For each domain, A and AAAA DNS records were used to identify associated IP addresses, which were then mapped to their routed BGP prefixes using longest prefix match. We used RIPE RIS and filtered to include only prefixes seen by at least ten peers, ensuring focus on widely visible routes. These prefixes were validated using RIPE NCC’s RPKI Validator and categorised as Valid (covered by a correct ROA), Invalid (conflicting with a ROA), or Not-Found (lacking any ROA). IP addresses that fell under Invalid or Not-Found prefixes, and were not concurrently covered by a more specific Valid ROA, were classified as being associated with IP addresses under RPKI Invalid or Not-Found prefixes.
The results point to varying levels of ROA adoption among the government domains in the analysed countries. The graph below shows the count of identified domains covered and not covered by ROAs.
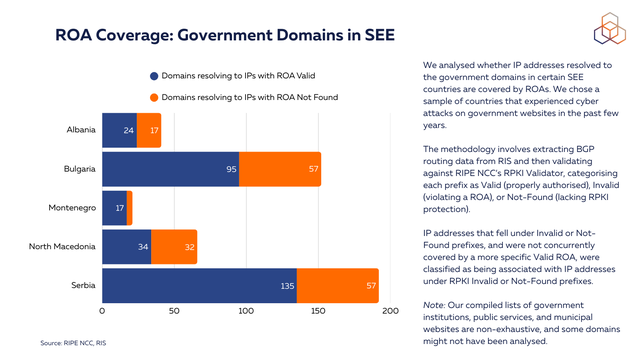
These preliminary findings should be interpreted with caution. The domain set is incomplete, and no assessment was made of the specific function or criticality of the services involved. It is possible that the most sensitive services are already covered by ROAs, while less critical domains remain associated with IP addresses under RPKI Invalid or Not-Found prefixes. Nevertheless, the results highlight the uneven progress of RPKI deployment across the region and suggest that further attention to routing security is warranted. We are planning to expand the dataset and include a broader range of government and public service domains, as well as critical infrastructure such as banking, healthcare, and telecommunications. Analysing the operational role and relative importance of each domain will also help in assessing the real-world risks posed by insufficient ROA coverage.
ROV
After creating ROAs, the critical next step in strengthening RPKI-based routing security is deploying Route Origin Validation (ROV). ROV ensures that BGP route announcements comply with the authorisations specified in ROAs, effectively mitigating both malicious prefix hijacks and accidental misconfigurations.
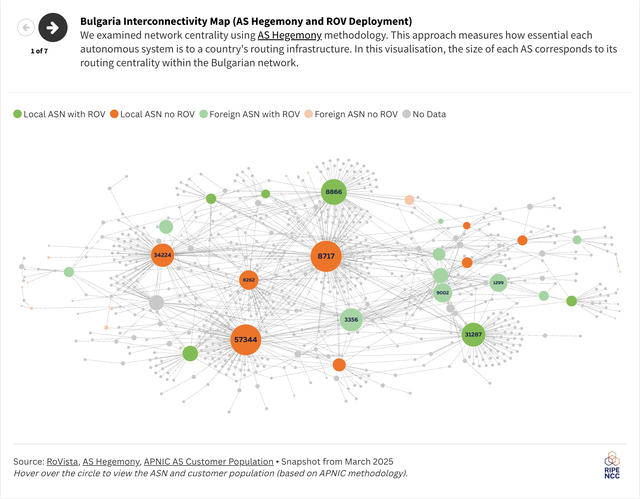
We used RoVISTA, a tool that assigns scores based on the ability of an autonomous system (AS) to reach prefixes marked as RPKI-invalid, to assess ROV deployment across the region. Specifically, we examined whether key networks identified as central to the routing infrastructure in our previous report have begun to implement ROV.
Network centrality was evaluated using the AS Hegemony methodology, which quantifies how essential each AS is to a country's overall routing infrastructure. In the visualisation below, the size of each AS reflects its routing centrality within the respective country's network. The visualisation provides an integrated view combining network centrality (AS Hegemony) with ROV deployment status (RoVISTA scores) for Bulgaria, Greece, Montenegro, and Serbia.
Our analysis found no significant region-wide changes since our previous report. However, notable positive developments include Lancom (AS199081), the host of last year's SEE meeting, and global telecom provider TI Sparkle (AS198477). These networks, or their upstream providers, have now started to deploy ROV, thereby enhancing routing security for their downstream networks.
To clarify the interpretation of these results:
- ROV Deployed: Indicates that either the AS itself or at least one of its upstream providers has implemented ROV. This significantly improves protection against using hijacked or accidentally misconfigured routes and increases overall routing security for the AS and its downstream networks.
- ROV Not Deployed: Indicates that neither the AS nor its upstream providers have implemented Route Origin Validation (ROV). Consequently, the AS and its downstream networks are vulnerable to accepting and propagating invalid route announcements, resulting from route hijacking or accidental misconfigurations, potentially causing traffic disruption or malicious interception.
The highlighted cases of Lancom and TI Sparkle illustrate the broader impact of deploying ROV in centrally positioned networks. When central ASes deploy ROV, they extend protection to all downstream networks that rely on them, thereby substantially improving national and regional routing security. Strengthening routing security through widespread ROV adoption is thus a crucial layer in the overall cybersecurity posture of any network.
IPv6 capability and adoption
Another important aspect we are going to cover is the IPv6 adoption in the region. With the growing digitalisation and expansion of digital services in the region, IPv6 becomes an essential technology to meet the demand of growing networks. We analysed the dynamics of IPv6 allocations, capability, and adoption for the past year.
From the IPv6 allocation perspective, we observed that allocations are often proportional to the number of active Local Internet Registries (LIRs) for each country. Romania and Bulgaria still hold significantly higher amounts of active LIRs when compared to other SEE countries and also lead by a wide margin when it comes to a number of IPv6 allocations.
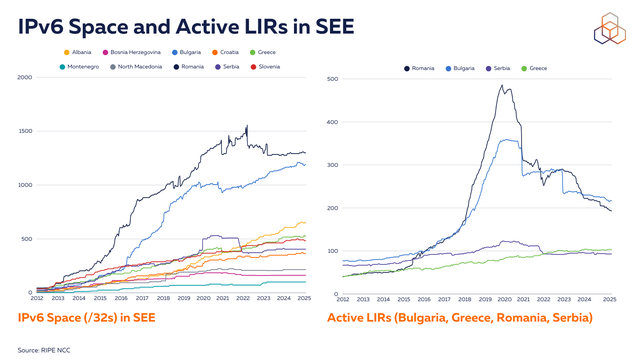
IPv6 capability, defined as the percentage of ASNs routing at least one IPv6 prefix, remains low in the region (24%) compared to the EU average (around 38%) (see graph below). Given the vast size of the IPv6 address space, merely counting addresses would not provide a meaningful metric. Instead, we focus on the advertisement of prefixes by Autonomous Systems (ASes) as a key indicator of IPv6 capability. This is similar to last year’s results which suggests that no major changes in terms of announcing IPv6 space in the global routing have been observed. Meanwhile, the IPv6 allocations and the number of active LIRs in Romania and Bulgaria showed a downward trend for the past year (see graph above).
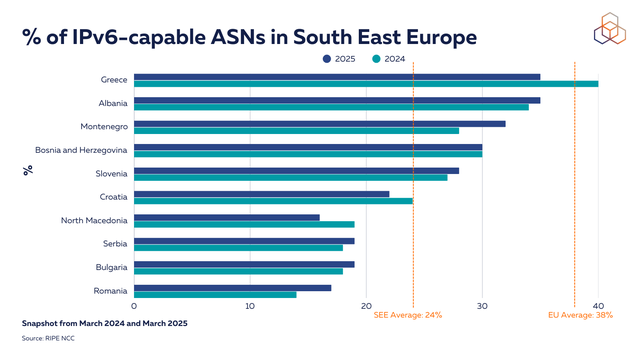
Greece remains the leader in IPv6 capability in the region, although the overall percentage dropped from 40% to 35% primarily due to some ASes stopping IPv6 announcements or transitioning to IPv4-only. Specifically, five IPv6-capable ASes stopped announcing IPv6, and seventeen new ASes started announcing only IPv4 prefixes, outweighing the few ASes that gained IPv6 capability. At the other end of the scale, Bulgaria and Romania have the lowest percentage of ASes announcing IPv6 space in global routing.
While IPv6 capability indicates that IPv6 addresses are being routed, this does not equate to adoption. Addresses may appear in global routing tables but might not be actively utilised internally by providers. So, to get a better handle on real IPv6 usage, we examined Content Delivery Network (CDN) data showing the percentage of users accessing content over IPv6. This metric provides insight into actual end-user IPv6 adoption, revealing how much IPv6-capable infrastructure is being actively utilised. The comparison between capability and CDN-based adoption metrics helps identify gaps between infrastructure readiness and practical implementation, highlighting where additional effort might be needed to drive IPv6 utilisation.
Recent data from major CDNs reveals varying levels of IPv6 adoption across the region. Greece is leading with a high level of IPv6 adoption across Google (63%), Facebook (56%) and Cloudflare (38%). It is followed by Romania with IPv6 adoption ranging between 18-33%. Google and Cloudflare also provide the metrics for Kosovo. According to Cloudflare, the IPv6 adoption in Kosovo is 18%, while for Albania it is 1%. Meanwhile, Google reports 0% adoption for Kosovo and 10% for Albania.
| Country | IPv6 adoption (Google), % | IPv6 adoption (Facebook), % |
IPv6 adoption (Cloudflare), % |
|---|---|---|---|
| Greece | 63 | 56 | 38 |
| Romania | 32 | 33 | 18 |
| Bulgaria | 21 | 15 | 6 |
| Slovenia | 14 | 13 | 8 |
| Albania | 10 | 8 | 1 |
| Bosnia Herzegovina | 10 | 15 | 6 |
| Croatia | 9 | 5 | 4 |
| Serbia | 6 | 7 | 5 |
| Montenegro | 0 | 0 | 0 |
| North Macedonia | 0 | 0 | 0 |
| Kosovo | 0 | 18 |
Conclusion
The SEE region continues to make important strides in strengthening its Internet infrastructure in the areas of routing security and IPv6 deployment. Our analysis shows that while many networks in the region have achieved high levels of ROA coverage - especially for IPv4 space - there is still considerable room for improvement, particularly in the deployment of ROV and the coverage of IPv6 space. The positive steps taken by key central networks to enable ROV signal a growing awareness of the importance of secure routing practices.
While cybersecurity remains a key concern in the region - especially following recent waves of cyberattacks - this article focused on a different, but equally important, layer of protection: routing security. RPKI does not prevent cyberattacks or protect websites from being compromised. However, it plays a crucial role in securing the global routing system and preventing incidents like route hijacks and traffic interception, which can amplify the impact of cyber threats.
As digitalisation continues to grow, ensuring the resilience of Internet infrastructure requires both solid cybersecurity policies and strong technical measures. Expanding ROV deployment and closing the gap between IPv6 capability and adoption will further strengthen the region’s Internet stability and security.
If you’re interested in the Internet in South East Europe, join us for the upcoming SEE 13 meeting that will take place in Sofia, Bulgaria, on 7-8 April 2025. Register on the meeting website.





Comments 0
The comments section is closed for articles published more than a year ago. If you'd like to inform us of any issues, please contact us.