You can view the slides, you can watch the recordings, but if you're wondering what's really happening at RIPE 86, read the daily meeting blog!
Day Five: It is no Longer Secret
Despite late-night fun on the boat, the attendees gathered for the last day of RIPE 86. It has been a great week with 863 attendees onsite (our highest so far) and 216 joining online. What a big crowd!
We’ve been through fire alarms and clicker revolt, and indulged in some jazzy dancing and a variety of cheeses!
Plenary: Time Maps and VPN Mysteries
Jonas Mücke from TU Dresden started the morning Plenary session delving into the world of QUIC deployments and the use of passive measurements to gain insights. One of the attendees was wondering if their approach can work on IPv6. In principle it can but there is no known large-scale IPv6 telescope for now.
Claudio Allocchio and Fabio Farina introduced the GEANT TimeMap Jitter and Latency Monitoring Service, unveiling a hidden aspect of network monitoring. Their presentation highlighted the significance of monitoring network jitter and latency for ensuring optimal performance and reliability.
We further moved to the Lightning Talks. Willem Toorop from NLnet Labs investigated if we can determine which ASes really should start doing ROV. He concluded that a small group of organisations can make a big impact on routing security. Telecom Italia, we’re looking for you!
Are you annoyed that other regions have more content on your streaming services? Well, Etienne Khan from the University of Twente might have something for you. Etienne has researched how geo-unblocking via VPN works and unpuzzled the mystery of the traceroutes to netflix.com.
Have you tried to contact these companies yet?
The last Lightning Talk of RIPE 86 was by Tony Finch from ISC who tried to unveil the mystery of where his computer gets the time from.
-From a secret space force based in Colorado?
-Maybe! But where does this base gets the time from?
-From USNO (US Naval Observatory Washington DC) alternate master clock (and they get it from atomic clocks)
-Don’t they also get the time from IERS to keep UTC in sync with the rotation of the Earth?
-They get it from BIPM because they get official UTC from them…
(And then your Daily Meeting Blog author just got too confused…)
The Last Hours…
Moritz Frenzel from Globalways GmbH started the Closing Plenary with his presentation on Redesigning an OOB Network. Moritz spoke about the operation of their network focussing on their 19 Main POPs. He discussed the issues they faced with their old OOB network and gave an overview of redesigning the network aiming to reduce the footprint, operational complexity, and reliance on VPN concentrators.
Rob de Meester presented the traditional RIPE 86 Technical Report. An open question to the audience from the tech team: Should we turn off the NAT64 network?
They then dived into the presentation system and of course, presented the coffee stats! 4,544 and 4,700 espresso shots were consumed in Rotterdam. It is more than in Berlin but seems like the per-person coffee intake has dropped.
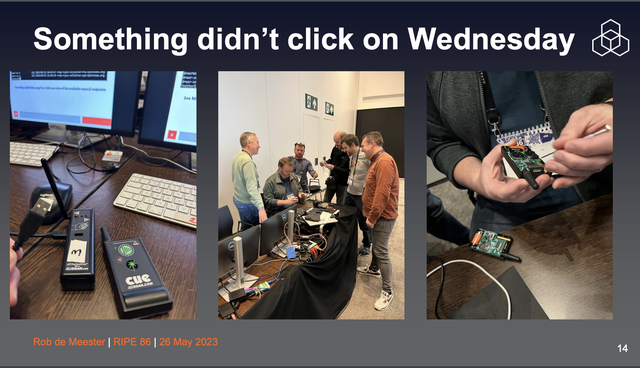
How many engineers does it take to change the channel on a clicker?
After the Tech report, the newly appointed RIPE Code of Conduct (CoC) Team presented their first report. Cynthia Revström reminded the audience that you can report to the CoC team via form or email, or in person to an individual team member, and the call for volunteers is still open.
Well, there is no Closing Plenary without a round of new appointments and goodbyes to some people. RIPE Chair Mirjam Kühne announced Clara Wade and Doris Hauser became our two new members of the RIPE Programme Committee (PC) and thanked Franziska and Milad for their incredible job as PC members.

Thank you, RIPE PC!
Congratulations also to our new Working Group Co-Chairs, Ben Cartwright-Cox (Routing WG) and Peter Wehrle (IoT WG) and thank you to the outgoing Co-Chairs Job Snijders and Sandoche Balakrichenan!
It is no Longer Secret
Well, it is no longer a secret… The Public Working Group took over the stage as the secret of the Secret WG spilled out…

Which Chair would you select?
And then, we were not allowed to write anymore… for some reason…
Not secret-wg anymore... 🤣#RIPE86 pic.twitter.com/NEXtk2VitB
— Clément Cavadore (@acontios_net) May 26, 2023
Dankjewel Rotterdam 🇳🇱 #RIPE86 was great! See you all in Rome 🇮🇹 at the end of the year for #RIPE87. pic.twitter.com/qLm756Whs1
— Philip Berndroth (@pberndro) May 26, 2023
Tony Finch @fanf is digging up where all those respectable clock management institutions are getting their time from #RIPE86 pic.twitter.com/UEhJ9mNfpo
— Dmitry Kohmanyuk (@dk379) May 26, 2023
Day Four: More Working Groups, Community, Diversity, and FIRE!
Day two of WG sessions at RIPE 86. Another day of two tracks of working groups, this time with a bonus intermission.
DNS
At the RIPE DNS Working Group, Andronikos Kyriakou introduced the DNS4EU project, which aims to provide secure and compliant DNS resolution for 100 million users across Europe. The project focuses on privacy, resilience, and cross-disciplinary collaboration, and offers protection against global and local threats. Shane Kerr then gave an update from the recently-formed DNS Resolver Best Common Practices Task Force – still early days, but the next step for the group is to publish a draft RIPE Document and ask for feedback from the RIPE community. Geoff Huston looked at the DNS4EU initiative from a measurement perspective. Philip Homburg presented on software that originates DNS queries, focusing on setting up TCP or TLS connections, presenting an idea called Connectbyname, a library call that simplifies the process for applications. Matthijs Mekking talked about DNSSEC multi-signer models, Anand Buddhev gave an update from the RIPE NCC and Stefan Ubbink gave an update from the DNS Hackathon that was held the weekend before the RIPE Meeting.
DNS WG at #RIPE86 pic.twitter.com/Oyjh8SjRtK
— 「𝗠𝗮𝗿𝗰𝗼」🐕🚶🏼 (@marcodavids) May 25, 2023
MAT
Over in the Measurements Analysis and Tools session, Marco Polverini introduced a digital twin-based framework that moves beyond the traditional "tweak and pray" approach to predict BGP configuration outcomes. Romain Fontugne demonstrated the ambitious Internet Yellow Pages project, simplifying access to network resources through a centralised knowledge graph. Yevheniya Nosyk addressed the issue of DNS query manipulation in the wild and potential measures to avoid it. Lastly, Nurullah Demir highlighted the importance of websites updating their software for better security as 94% of websites contain at least one vulnerable software.
Where would we be without our fabulous stenographers? Luckily it was just a false alarm🔥 #RIPE86 pic.twitter.com/VZDBEemN2O
— RIPE 86 - Rotterdam, the Netherlands (@ripemeeting) May 25, 2023
Brief interlude...
At some point during the above sessions we got an opportunity to stretch our legs, and a test of our responsiveness to audio stimuli and ability to amble in the general direction of safety should the need ever arise. B+ in the opinion of this humble scribe.
Connect
The session started with Louis Pétiniaud from Geode on mapping the geography of the Internet in Central Asia. Louis explained the mapping methodologies used (physical infrastructure, BGP feeds, RIPE Atlas) and how they augmented this with field work (interviewing local stakeholders and performing on-site traceroute measurements).
Stavros Konstantaras from AMS-IX presented work by several IXPs to create a common policy for where route server participants should publish their filtering rules. The third presentation was by Silas Peprah from PAIX, who described the development of the Internet in Ghana and introduced Accra-IX. Finally, Leo Vegoda (PeeringDB) and Bijal Sanghani (Euro-IX) gave updates on their respective initiatives.
IPv6
Tayfun Ozaltin, from the RIPE NCC’s Learning and Development team, asked for input from the WG on an advanced e-learning course they were developing. Rinse Kloek, from Delta Fiber / Kindes, shared some of the challenges they encountered in their move to IPv6. Wilhelm Boeddinghaus’s from Route 128 asked if the community could provide clear guidance on IPv6 deployment phases and challenges, especially for enterprise IT departments. Fernando Gont, from SI6 Networks gave a remote presentation on some of the security challenges that accompany IPv6 deployment.
WG Co-chair Benedikt Stockebrand announced that he would not be standing again after the end of his term (thanks Benedikt!) And finally, Ondrej Caletka from the RIPE NCC’s tech team asked attendees to try out the IPv6-only meeting network to identify issues that could be reported to vendors.
Open Source
Niall O’Reilly started the session by talking about NGI-Zero, an EU project to improve the Next Generation Internet. Next up was Guillaume Mazoyer, who shared his experiences with moving the ix-api into a library. Ondřej Zajíček then shared the history of the BIRD project up till now and what to expect for the next version of BIRD. Niels Rainer then presented on the Route Server Support Foundation and its support on OpenBGPD.
The presentations were concluded with lightning talks by Maria Matejka on BIRD GUI and Alastair Strachan on the RIPE Community Projects Fund. The session ended with Ondrej Filip announcing that he was stepping down as working group chair.
Database
Edward Shryane gave an update from the RIPE NCC. Some upcoming changes: Client Certificate Authentication (HTTPS), Cleanup of “remarks:” attributes, RDAP Redacted Fields and RDAP RIR Search. Ed also noted that they would be looking into the use of cloud infrastructure, using their updated Cloud Strategy and Service Criticality frameworks to inform a proposal that they would share for community input. Denis Walker, DB WG Co-chair then proposed a change to the way that the RIPE Database is managed which takes into account the fact that everyone’s busy and often there is low levels of feedback on various proposals in the WG. Finally, Maria Stafyla from the RIPE NCC gave an update on RIPE Database use cases.
RIPE Community Plenary
In the community plenary, Mirjam Kühne announced that the Code of Conduct TF had finished its work and thanked the group for its work to get the required documentation and team in place. Falk von Bornstaedt gave an update on the 2023 Rob Blokzijl Award, noting that the award committee would soon issue a call for nominations. The foundation is also accepting donations. Leo Vegoda then raised some very pertinent points about the future of mailing lists - noting that most email passed through just two email providers, and discussion lists suffered when legitimate emails were treated as spam. Does the community need to start planning long-term for a time where mailing lists are no longer viable? And should we be thinking about the younger generation, who might be less interested in this format of discussion?
Edward McNair, NANOG Executive Director gave an update from their community, Kim Davies gave the IANA update and Henrik Kramselund presented on the idea of creating a “newcomers guide to the Internet,” noting that some core concepts needed to be understood before you can read RFCs. He wants to compile a list of engaging materials. Commenter at the mic "I never give my new staff members RFCs to read while onboarding them… I don't want them to leave."
Diversity in Tech
The last session of the day and a topic that appears to have been steadily attracting more attention over successive RIPE Meetings: diversity in tech. Four panelists from NANOG, IETF, Wikimedia and Internet Governance communities shared their perspectives, emphasising the importance of intergenerational inclusivity, creating pathways for underrepresented groups, and embracing diverse voices and perspectives.
The session also discussed the challenges faced by young professionals in attending conferences – with cost being identified as a huge barrier. Solutions could be fellowships, virtual attendance options, and sponsorships from companies. The importance of mentorship, creating opportunities for junior staff, and promoting gender diversity in leadership roles was also highlighted.
Time for the diversity in tech panel #RIPE86 pic.twitter.com/WGPFycX6DG
— Chris (#RIPE86) (@connectChris) May 25, 2023
Day Three: Cake and Stroopwafels for the Working Groups!
The day is split into two parallel tracks, where each Working Group (WG) can dive into specific topics – here’s a rundown.
Routing
Ties de Kock kicked off the session with a milestone announcement of 20,000 RPKI certificates, reflecting the increasing adoption of RPKI. Alexander Brundiers came up next and presented his research on routing and traffic engineering, highlighting the use of midpoint optimisation. Job Snijders introduced RPKIviews, a project addressing RPKI data archiving, and sought community support for its development. The final presentation came from Ben Cartwright-Cox, who presented his findings after one year of announcing real-time bgp.tools. The session closed with Job Snijders stepping down as co-chair of the WG (thank you, Job, for your service!) and passing the baton to Ben - congratulations!
Newly appointed co-chair Ben Cartwright-Cox celebrates the 20,000 RPKI certificates landmark with cake!
Cooperation
Benjamin Broersma introduced the Dutch Internet Standards Platform, which promotes modern Internet standards such as IPv6, DNSSEC, HTTPS, HTTPS security headers, DMARC+DKIM+SPF, STARTTLS+DANE and RPKI. The Cooperation WG Task Team described their response to the European Commission consultation on the future of the electronic communications sector and its infrastructure in which they advise against a mandatory payment mechanism to avoid termination monopoly, which would then necessitate regulatory oversight. Finally, Natalia Filina called for deeper collaboration between the RIPE Community and EURALO, ICANN’s European regional at-Large organisation.
Address Policy WG (Sessions 1 and 2)
The WG held a discussion on the structure and a proposal to change the term limits for new chairs. The intention is to introduce more stability and improve the rotation schedule. Additionally, there was an active discussion on several key topics:
- Temporary Transfer Policy: The similarities between temporary transfers and other forms of leasing, whether it should be possible to extend the duration of a Temporary Transfer, and how to address concerns relating to implementing RPKI and creating ROAs.
- Out-of-region AS Number Assignments: Why the policies in the RIPE region are more liberal than those in other regions and whether AS Assignment policies should be brought in line with PI Assignment policies.
IoT
The session opened with an insightful presentation by Lennert Bober, who discussed the properties of optical wireless communications for IoT devices and explored its potential for future mass market usage. Maarten Bottermann then shared valuable insights on sharing global good practices in the IoT domain, addressing critical challenges like ethical applications, trustworthiness, sustainability, and deployment. The WG also deliberated on potential changes to its charter and the possibility of closer collaboration with other working groups. Lastly, the group expressed gratitude to Sandoche Balakrichenan for their dedicated service as co-chair and warmly welcomed Peter Wehrle as the new co-chair.
Anti-Abuse
The WG session started with a training update from Gerardo Viviers and continued with recommendations from the RIPE Database Task Force. Theodoros Fyllaridis came up on stage to present the manner in which the RIPE NCC handles LEA requests and the data it provides. His presentation received a lot of interest from participants, and we have compiled some thoughts from Twitter users:
.@ripencc provided their LEA Transparency Report 2022 as part of the Anti-Abuse Working Group session during #RIPE86 – thank you!
— Robert Scheck (@robertscheck) May 24, 2023
Personally, I even would like to see the actual LEA requests (sensitive information redacted) publicized; see examples at https://t.co/B89IckhW7t pic.twitter.com/nLKCV27p4G
Still not the best at following procedures... French LEA keeps asking information requests to @ripencc that does not involve RIPE NCC... (121/186 LEA requests !) #RIPE86 #antiabuse https://t.co/0oGv1aeEUf https://t.co/2EriYY49Ng pic.twitter.com/GQTzR1F05I
— Vincent Zafra (@vzafra) May 24, 2023
RIPE NCC Services
Hans Petter Holen presented the RIPE NCC activities of 2023 and touched on the plans of what happened in the past four years that impacted the RIPE NCC operations. He then proceeded to present the RIPE NCC activities and budget for 2023, with a look towards the upcoming three years. Felipe Victolla presented the RIPE NCC Registry and Technology Update. He then proceeded to listen to comments and answer questions from the audience about different topics: including in the next update stats on the recovery of address space from PI assignments, any possible additional burden on the Registry from implementing NIS2, and the Cloud Framework used by the RIPE NCC.
Fergal Cunningham explained the usefulness of the results of the RIPE NCC Survey carried out every 3-4 years. He presented some statistics on the number of questions in the survey and announced that the survey is open now for everybody to participate. Sander Stefan presented the proposal to add a voluntary transfer lock to the number of resources registered with the RIPE NCC. This proposal treats the transfer lock as a service from the RIPE NCC, and Sander explained why it is not being discussed in the Address Policy WG. Christian Kaufmann presented the type and amount of work an Executive Board (EB) member is expected to do. He did a recap on the different situations over the past 12 years that he had to face as an EB member, which can help future EB members to understand what the expectations for them will be.
Wrap Up
The day ended with a Stroopwafel stand as participants got ready for the General Meeting. More WG sessions are starting tomorrow morning - tune in!

Day Two: Bogons, Martians and Salt Minions
No, you’re not reading a sci-fi novel – this is the story of the second day of RIPE 86, where we explored the mysteries of time and looked into the future of regulation, protocols and AI. We also explored the mysteries of cheese in a delectable Cheese BoF.
A Very RIS-y Morning
We started with two Plenary talks giving insights into routing. First, Khwaja Zubair Sediqi of the Max Planck Institute for Informatics shared how he used route collector data to investigate hyper-specific prefixes. Then Alexandros Milolidakis of the KTH Royal Institute of Technology explained to us how attackers can avoid detection when carrying out BGP hijacks. We at the RIPE NCC were thrilled to see that both talks referenced data from our very own route collector project, RIS. Finally, Massimo Candela of NTT taught us about geofeeds as a solution to problems with geolocation. His presentation generated a lively discussion about whether the community should even want things like accurate IP geolocation—something for us all to ponder this week.
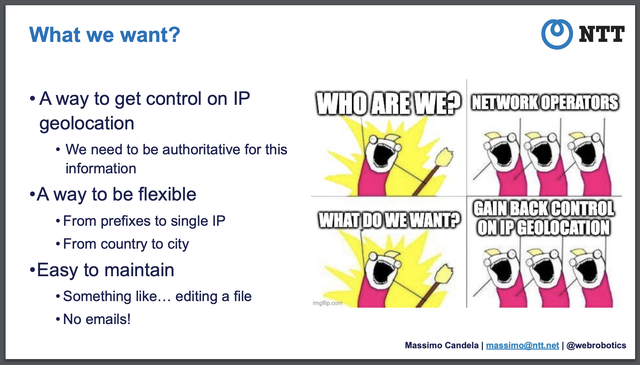
Massimo’s succinct analysis of our geolocation needs
Developments in Regulation and Protocols
Our second Plenary session of the day turned to EU regulation. Benno Overeinder of NLnet Labs, Bastiaan Goslings of the RIPE NCC and Robert Carolina of ISC came together to explain the Proposed Cyber Resilience Act and Product Liability Directive, which both aim to regulate open source software. This could have far-reaching legal consequences for developers by making them liable for whatever products are built off of their software. So open sourcers, watch this space!
Cheese: a delicious dairy product and also a useful metaphor
Next, Bart van de Velde of Cisco took us through the new reality of the rising protocol stack H3/Quic/UDP/DOH. QUIC now forms a significant part of the traffic on major apps throughout the world. This encrypted stack has various implications for networking, from how videos are downloaded and streamed to how the time domain is shaped. Bart advised a scalable, IP flow-centric approach for networks to adapt.
Then we were treated to three lightning talks. Elisantila Gaci of the National Technical University of Athens taught us all about configuring WiFiMon probes. WiFiMon, a WiFi monitoring and performance verification system, uses measurements from hardware probes called Salt Minions to gather performance data. Next, Lefteris Manassakis of Code BGP gave us a peek into the mysterious world of bogons and how to monitor them. Bogons are a type of prefix; they include both prefixes that have not been allocated and martians, which in this case are private and reserved addresses, not little green men. Finally, Peter Thomassen of deSEC taught us how to use deSEC to make DNSSEC more secure.
The Parallels Between RPKI and Spaghetti
IPv6 extension headers are back in fashion, according to Ana Custura of the University of Aberdeen, with headers being used for packet telemetry and to run measurements. However, they currently work in some mysterious ways. Ana's experiments showed that extension headers work if they’re small enough, but we don’t know why. They also work differently over TCP and UDP, but again, we’re not entirely sure why…If you know the answer, Ana will buy you a beer.
Geoff Huston of APNIC presented us with the challenge, to DNSSEC or not to DNSSEC? After all, if it’s so great, why aren’t major enterprises like Google, Facebook, Microsoft or Amazon using it? There are two sides to every argument, and Geoff presented both. There are some strong reasons not to use DNSSEC, as anyone who has ever lost keys (real or digital) will attest to. And there are equally compelling reasons that make it useful—DNSSEC can offer a lot of features of certificates without the intermediaries. Geoff, however, has some ideas as to how we can rethink DNSSEC at the application layer rather than at the platform level. L’enfer, c’est le DNSSEC, said Sartre never.
Randy Bush of IIJ Research and Arrcus Inc began by thanking the RIPE PC, RACI and the community for the absence of vendor presentations. Then he took us through the complicated world of RPKI.
In the wisdom of Randy, RPKI may be built from simple elements but forms a complex whole—much like the plate of spaghetti seen here
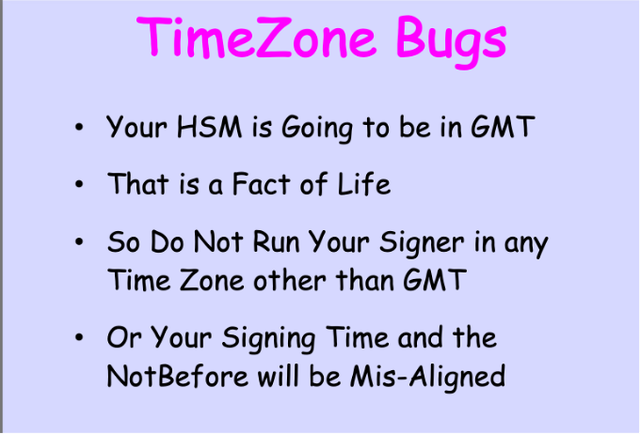
Amid this complex spaghetti of a system, Randy highlights a fresh issue – time zones (which anyone suffering from jetlag at RIPE 86 will sympathise with). Problems with time zones include that some RIRs have their HSMs in GMT but sign their time zones in local time. Another is that BGP propagates in minutes, but RPKI propagates in an hour.
Here’s some wisdom from Randy, in his signature style:
Incident and Risk Mitigation
In our last Plenary of the day, Tom Strickx of Cloudflare explained incident management (and yes, the major Cloudflare outage last year did come up). The three-step management process requires detection, mitigation and remediation, and reporting.
As Tom Strickx demonstrates, it’s difficult to create a product but easy to find problems with it
In the final talk of the day, Giovane Moura of SIDN Labs continued the topic of mitigation, specifically mitigating risks in e-gov domains. Sadly, it seems many e-gov domains are not following recommendations that reduce unnecessary risk, like avoiding single points of failure. As Giovane reminds us, don’t put all your eggs in one basket, or one DNS provider, as the case may be.
Cheese and ChatGPT
And finally, we came to our BoFs. One session was the IETF Overview of Technical Work and Hot Topics, which brought everyone up to speed with the work of the IETF and how they could participate. In another BoF session, The Impact of the Latest Developments in Artificial Intelligence on the RIPE Community, one key topic was ChatGPT and its implications. Rather than sum up the discussion ourselves, let’s hear from ChatGPT about what happened:
“The AI BoF session at RIPE turned up the excitement as network engineers dived into the impact of AI on their community. From hilarious revelations that "there are no secrets in RIPE!" to pondering whether AI could generate an entire RIPE Meeting, the atmosphere was buzzing. Discussions covered AI's quirks, like not knowing which RFCs to implement, and its newfound ability to spare people's feelings. Attendees shared fascinating stories, like Germany's tax authorities benefiting from AI (although the clever Swedes were ahead of the game!). We also uncovered the challenges of running AI at home and the potential domination of big tech companies. The session sparked curiosity, highlighting the need to consider social scientists' insights and legal perspectives. It was a whirlwind of excitement, showing that AI integration is anything but boring!”
Last but not least, there was a very special session, the Cheese BoF. In an inspirational act of culinary diplomacy, attendees brought in cheeses from their home countries for others to try.

RIPE 86 attendees treating themselves to a vast array of diverse cheeses
After the sessions of Day Two, it was onto Maassilo for our networking event. That’s all for now—tune in tomorrow!
Tuesday’s Top Tweets
We feel seen #RIPE86 pic.twitter.com/3V1oDOvBGT
— Mick Begley (@mickarooney) May 23, 2023
DNS appreciation
The Dutch are really nerds… #ripe86 pic.twitter.com/nPclysHdIF
— 🇨🇭Pascal Gloor (@spale75) May 22, 2023
MPLS: routing traffic using the shortest path, online and off
Quick stop before leaving for @ripemeeting’s #RIPE86: getting some cheese from my hometown for the @nlnog Cheese BoF. Found some flavored with beer from the local brewery Brouwerij de Molen 🧀 pic.twitter.com/oYCDlIGAlP
— Teun Vink (@teunvink) May 23, 2023
Preparations for the Cheese BoF: the tastiest of RIPE 86 sessions
Day One: Nordic Rivalries Take Over RIPE 86
Welcome to the RIPE Meeting at Rotterdam Ahoy, the famed Eurovision song contest venue, which now has the pleasure of hosting a RIPE Meeting. Eurovision was last week, and saw Sweden’s Loreen narrowly beat Finland’s Käärijä among whispers of jury-rigging…
In another Eurovision coincidence, not only is it 50 years since ABBA won the coveted crystal mic, it’s also 50 years since the invention of Ethernet! You can first take a selfie with the Eurovision mic and then make your way up the RIPE 86 Ethernet staircase.
Welcome to RIPE 86...
RIPE Chair Mirjam Kühne welcomed everyone back to another RIPE Meeting. This promises to be another very full meeting week. Over 500 people were onsite on Monday, and with over 800 people expected to attend in total, the baristas will be kept very busy indeed.
Among other things, she pointed to the appointment of a Code of Conduct team, who are now empowered to take action against people violating the RIPE Code of Conduct. Thank you to the team for helping us have a safer environment at RIPE Meetings. Her slide deck took a curious twist, and she found herself delivering a message from a group of mysterious individuals who claim to represent a working group that shall not be named here. How they snuck that slide into the RIPE Chair’s slide deck remains a mystery, and the RIPE NCC is looking into it. If you email your idea, you will automagically hear back from the not-so-secret WG.

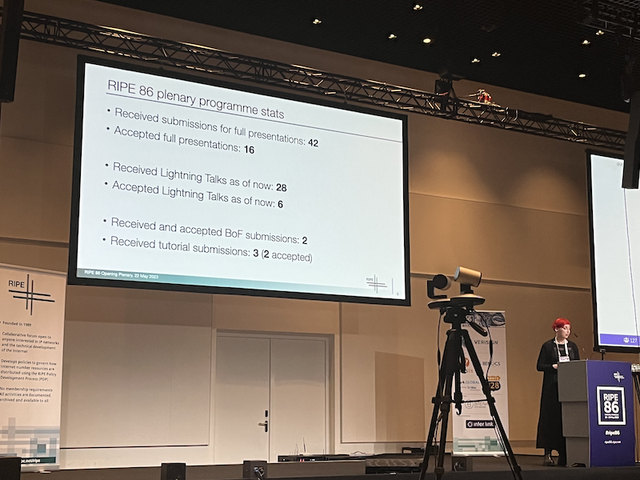
They say competition is increasing everywhere, and that was evident from PC Chair Franziska Lichtblau’s slides. Your talk has a one in three chance of being accepted for a RIPE Plenary and a one in six chance of being accepted for a lightning talk. Should that discourage you? Absolutely not! According to Franziska, you can still submit a lightning talk for consideration - and if you prefer awarding douze points, you can nominate yourself to be on the RIPE Programme Committee. There are two seats up for election at RIPE 86, and new candidates are welcome!
Hans Petter Holen, the RIPE NCC Managing Director, welcomed attendees, and since the RIPE NCC is local host, got a chance to make his pitch to the audience. He shared that the RIPE NCC has issued 19,995 RPKI certificates, will we make it to the milestone of 20,000 before the week is out? The Nordic rivalry that started off at Eurovision has spilled over into the RIPE Meeting - Hans Petter couldn’t resist pointing out that Norway has deployed more IPv6 than Sweden (but glossed over the fact that Iceland, Denmark and Sweden are all ahead as far as RPKI is concerned). If you need to see the evidence for yourself, check out the Nordic Internet Country Report. He also reminded attendees to respect the social distancing stickers, and “apologised” to Finland’s Julf Helsingius for not having black stickers to ask people to keep 5 metres distance.
The zombie debate and climate emergency
The plenary talks by Rudolf van der Berg and Vesna Manojlovic took a much more haunting turn (a bit like when the Czech Republic took to the stage during Eurovision 2023).
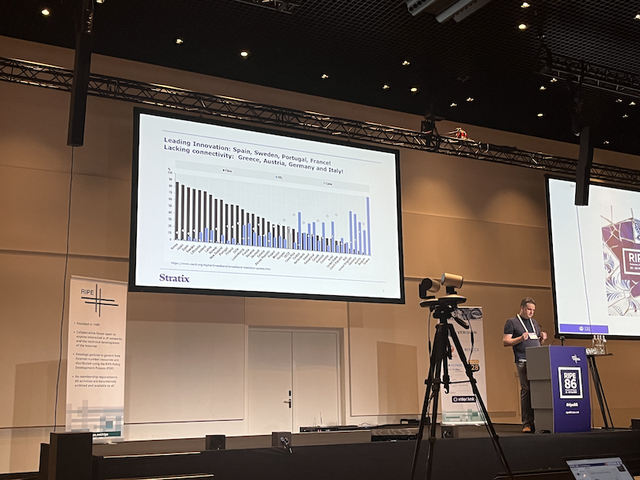
OTT and "sender pays" has been called the zombie debate - no matter how many times it's killed and put in the earth, it comes back to haunt the Internet community again and again. Rudolf van der Berg, Stratix went through some of the numbers and arguments provided by incumbent networks to see if they really added up. Apparently it's possible to find economists who'll argue that this whole peering and interconnection fad that the Internet's based on is fundamentally broken and what we really need is to go back to the grand old days of the telephony model. Incidentally, Rudolf also waded into the Nordic rivalry, showing a slide pointing out how Sweden leads in connectivity, followed by Iceland and then Norway.
If the revival of the sender pays debate isn’t enough to scare you, Vesna’s talk on the climate emergency will. She introduced the word ‘polycrisis’, defined as multiple overlapping catastrophic events taking place simultaneously. Her talk was a stark reminder that Internet operators have a role to play in responding to the climate crisis, and the lively discussion that followed showed that her point was not lost.
Time networks and lightning talks
Netnod’s Karen Ahl lost no time in talking about the importance of time, especially when it comes to network security. She explained that governments and regulators across the EU were focused on the importance of robust time, and how Sweden has developed an extremely accurate and secure time distribution network. In addition to Swedish Distributed Time (no, it’s not a new techno collective), Karin stressed the importance of the new Network Time Security standard
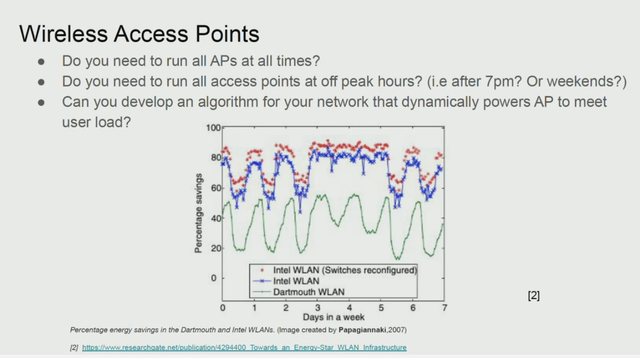
Climate is clearly on the agenda on Day One of RIPE 86, with Peter Ehiwe sharing research on techniques to reduce power usage. And he asked one really obvious question - do we really need blinking LEDs on devices when noone is actually working on it?
Olena Kushnir then took to the stage, sharing stories of courage and resilience from Ukrainian network operators, who are risking their lives to keep the country connected under the force of Russian bombardments. She also spoke about cyber-attacks and the theft of Ukrainian Internet number resources. This is a topic that is likely to come back in other discussions this week.
Clearly vying for the popular vote at RIPE 86, Florian Streibelt spoke about not one, but two of the RIPE community’s favourite topics in one short lightning talk - IPv6-only DNS resolution, opening with a warning “There is no IPv4 involved anywhere.”
We then moved on to the Best Current Operating Practices Task Force. Shane Kerr shared an update on the DNS Public Resolvers Task Force that has been looking into yet another aspect of EU legislation - on public resolvers. The DNS Task Force aims to provide a set of recommendations based on (no prizes for guessing) best practices for anyone seeking to set up a public DNS service.

Returning to the topic of Internet resilience (we suspect that along with EU regulation and AI, this is likely to be one of the most used terms over the week), RIPE NCC’s Alena Muravska continued the discussion started by Olena Kushnir. She pointed out that Ukrainian network operators are developing new methods to get their networks back online, and that these practices need to be documented to improve the resilience of the Internet in the face of extreme events. She called for volunteers to work with Ukrainian operators to help gather a “brain dump” of knowledge gained as a first step. And to the room’s credit, a few volunteers stepped forward to support documented best practices for extreme events.
With EU regulation, the climate crisis, IPv6, DNS, and Internet resilience discussed, Day One ended with a well-deserved welcome reception.
Monday's top Tweets
Here are our favourite tweets from today:
Brian Nisbet enters the Netherlands in style!
You're in the right place Lia, you're in the right place...





Comments 0
The comments section is closed for articles published more than a year ago. If you'd like to inform us of any issues, please contact us.