Encryption between DNS resolvers and users is growing - but what about the next hop? We measure the real-world deployment of encrypted resolver-to-authoritative DNS (ADoX), finding limited, highly concentrated adoption and little support among resolvers.
DNS encryption is on the rise. Proposed standards such as DNS-over-TLS (DoT), DNS-over-HTTPS (DoH), and DNS-over-QUIC (DoQ) are increasingly deployed between clients and recursive resolvers. In contrast, the recursive-to-authoritative link has long been overlooked, despite documented cases of traffic analysis and response injection by state censors.
Experimental RFC 9539 proposes a mechanism for resolvers to probe authoritative nameservers over DoT or DoQ (referred to as ADoT/ADoQ, or collectively ADoX) without prior coordination. Recent community efforts have focused on driving the adoption of this approach.
In this blog, we examine the deployment of ADoX in the wild, across both authoritative nameservers and recursive resolvers. For updates, follow the project website at adox-deployment.com.
Background on ADoX
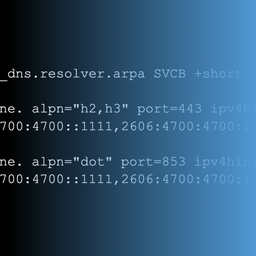
The proposed mechanism is unilateral (no prior coordination) and opportunistic (encrypts what would otherwise be sent in cleartext). DoT and DoQ both meet these requirements, as resolvers can attempt connections on the well-known port 853. DoH is explicitly left out of scope, as one cannot guess the path of the DoH endpoint.
Recursive resolvers probe nameservers via encrypted transports alongside standard Do53, logging both successful and failed connections. Authoritative nameservers must serve the same data regardless of transport. They may optionally add EDNS(0) padding to mitigate trivial traffic analysis, but do not need to provide any particular means of authentication. A self-issued X.509 certificate is sufficient.
DNS encryption should not be confused with DNS Security Extensions (DNSSEC). Encryption provides confidentiality, while DNSSEC adds data authentication and integrity. Therefore, these mechanisms are complementary.
How we measure deployment
We measure deployment at two levels - authoritative nameservers and recursive resolvers.
For nameservers, we compiled a comprehensive list of domains from multiple sources, including the IANA root zone database of top-level domains, ICANN's Centralized Zone Data Service (CZDS), passive DNS, and Certificate Transparency logs. We used zdns to map domains to NS records, then issued A/AAAA requests to obtain nameserver IPs. We then attempted ADoT and ADoQ connections to each nameserver, with no certificate validation as allowed by the RFC. Once we identify nameservers that support encryption, we resolve the domains they serve over the corresponding encrypted transport. A domain is considered ADoX-enabled if at least one of its nameservers returns a NOERROR response to an SOA query over ADoT or ADoQ.
For resolvers, we configured two domains - dot.adox-deployment.com and doq.adox-deployment.com - accessible only via ADoT and ADoQ. We targeted open IPv4 resolvers from the Open DNS API dataset and responsive hosts from the IPv6 Hitlist, requesting each IP to resolve a unique subdomain. This lets us map queries observed at our nameservers back to specific open resolvers.
We also used the RIPE Atlas platform, requesting each probe to resolve these domains via its local resolver to identify closed ADoX resolvers, if any.
ADoX at authoritative nameservers
We conducted our measurements in March 2026, covering the root, 1.4K TLDs, and over 331 million registered domains. Below we take a closer look at the deployment patterns.
Adoption rates
At the root server level, USC/ISI (B-root) has operated an experimental ADoT service for several years. H-root (U.S. Army DEVCOM Army Research Lab) enabled both ADoT and ADoQ in 2026. These two operators also provide ADoX for .arpa - the infrastructure TLD.
Five top-level domains - .cy, .arpa, .gr, .𝜺𝝀, and .kg - currently support recursive-to-authoritative encryption. Among them, .kg and .arpa support all ADoX combinations (ADoT and ADoQ over IPv4 and IPv6). The remaining TLDs provide ADoT over IPv4 only.
Only 3.1 million registered domains (0.93% of those tested) are reachable over ADoX. The ratio of nameservers accepting encrypted requests is even smaller - 2,585 IPs (0.32% of those tested). ADoT is the preferred transport, with just over 3 million reachable domains (IPv4 and IPv6 combined), compared to 2.2 million for ADoQ.
Notably, almost 2 million domains support all protocol combinations - ADoT and ADoQ over IPv4 and IPv6. As shown later, these deployments are driven primarily by a single provider.
Operator concentration
With only 2,585 nameservers serving millions of ADoX domains, adoption is likely driven by a small set of providers. We group nameserver IPs by organisation to identify deployment clusters. Table 1 summarises the results.
| Organisation | NS IPs | ADoT domains | Organisation | NS IPs | ADoQ domains | |
|---|---|---|---|---|---|---|
| 1. | One.com A/S | 24 | 1,962,493 | One.com A/S | 24 | 1,962,493 |
| 2. | JSC TIMEWEB | 9 | 394,068 | WEDOS Internet, a.s. | 5 | 255,548 |
| 3. | JSC "RetnNet" | 1 | 389,006 | NetActuate, Inc | 3 | 14,066 |
| 4. | WEDOS Internet, a.s. | 15 | 276,492 | Hetzner Online GmbH | 73 | 3,794 |
| 5. | Nazwa.pl Sp.z.o.o. | 6 | 150,875 | Naquadria S.R.L | 1 | 2,937 |
ADoX deployment is highly concentrated. One.com accounts for nearly 2 million domains, all consistently reachable over both ADoT and ADoQ. WEDOS shows a similar pattern, supporting both protocols. Timeweb (JSC TIMEWEB and JSC "RetnNet") ranks second by ADoT domains but, like Nazwa.pl, does not support QUIC. We also observe what appears to be infrastructure rental or colocation for custom authoritative deployments: 73 Hetzner-hosted nameservers serve 3,794 ADoQ-enabled domains.
Public claims of ADoX support remain limited. Among the top five providers, only Nazwa.pl Sp.z.o.o. and WEDOS publicly acknowledge ADoT or ADoQ support in some of their products.
Next, we group ADoX nameservers by their registered domain name (e.g., ns1.one.com, ns2.one.com, and ns3.one.com become *.one.com). Table 2 shows that the ranking is dominated by the same provider seen in the IP-level analysis. One.com with its *.one.com, *.hostnet.nl, and *.antagonist.* nameservers (the two companies it previously acquired) drives the ADoT and ADoQ deployment. We also see operators use different top-level domains for resiliency, such as wedos.eu, wedos.cz, and wedos.com.
Overall, no aggregation approach is perfect - while IP-level analysis may point to infrastructure reuse within cloud providers (e.g., Hetzner), domain-based aggregation may fragment a single operator across multiple suffixes/TLDs. Therefore, no single approach fully detects operator boundaries.
| Operator | ADoT domains | Operator | ADoQ domains | |
|---|---|---|---|---|
| 1. | *.one.com | 1,437,545 | *.one.com | 1,437,545 |
| 2. | *.timeweb.ru | 400,684 | *.hostnet.nl | 396,138 |
| 3. | *.timeweb.org | 400,651 | *.wedos.cz | 255,218 |
| 4. | *.hostnet.nl | 396,138 | *.wedos.eu | 255,090 |
| 5. | *.wedos.cz | 269,645 | *.wedos.com | 254,984 |
| 6. | *.wedos.eu | 269,474 | *.g1-dns.com | 84,931 |
| 7. | *.wedos.com | 269,246 | *.g1-dns.one | 84,931 |
| 8. | *.nazwa.pl | 150,812 | *.antagonist.nl | 43,879 |
| 9. | *.g1-dns.com | 84,931 | *.antagonist.net | 43,879 |
| 10. | *.g1-dns.one | 84,931 | *.desec.org | 13,978 |
Domain popularity
We assess whether ADoX is deployed among popular domains, as high-traffic services impact disproportionately more users than thousands of lesser-known sites. Using the Tranco top 1 million list, we find only 5,688 ADoX domain names. Table 3 shows the top 10 highest ranked domains for ADoT and ADoQ.
The ADoT ranking is dominated by popular Meta-operated domains, such as facebook.com, whatsapp.net, or cdninstagram.com. In contrast, the most popular ADoQ domain appears at rank 147, followed by loteriadehoy.com (1,713) and one.com (2,006).
| Rank | ADoT domain | Rank | ADoQ domain |
|---|---|---|---|
| 5. | facebook.com | 147. | one.one |
| 12. | instagram.com | 1713. | loteriadehoy.com |
| 15. | fbcdn.net | 2006. | one.com |
| 27. | wikipedia.org | 3901. | eu.org |
| 41. | whatsapp.net | 6284. | sport1.de |
| 55. | whatsapp.com | 8769. | hostnet.nl |
| 80. | wa.me | 9961. | lectio.dk |
| 105. | root-servers.net | 10367. | digitalaudience.io |
| 109. | cdninstagram.com | 15342. | wedos.cz |
| 121. | cdn77.org | 16899. | bloggersdelight.dk |
Distribution among top-level domains
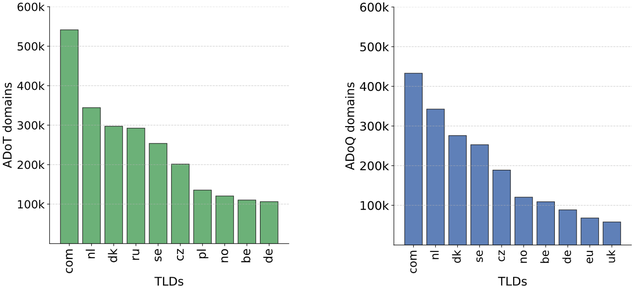
The 3 million ADoX domains span 774 TLDs. Figure 1 shows the top ten. Despite this seeming diversity, One.com is the dominant host of ADoX domains across all but three TLDs.
Notable exceptions include .cz and .ru, where over 99% of domains are served by WEDOS and TIMEWEB, respectively. For .pl, Nazwa.pl is authoritative for 84% of ADoT domains.
Fully-encrypted resolution paths
Encryption is only effective if applied at every step of the DNS resolution chain. We check for fully-encrypted paths where each nameserver, starting from the root, supports some combination of ADoX. We recall that stub-to-recursive encryption is also required for full privacy, but that falls outside the scope of this research.
In theory, all domains under .kg could be resolved exclusively over ADoT or ADoQ (IPv4 and IPv6), given ADoX support at both the root (H-root) and the TLD. In practice, our Internet-wide scan detected only 14 .kg registered domains supporting all ADoX combinations.
Relaxing the requirement to any ADoX combination, we identified 845 domains that can be resolved entirely over encrypted transport across the four ccTLDs (excluding .arpa) that deploy ADoX. This is a lower bound, as zone data is unavailable for most ccTLDs, limiting our initial domain dataset. Even so, the great majority of registered domains do not have a parent supporting ADoX.
ADoX at recursive resolvers
Our April 2026 scan found no open or closed resolvers capable of resolving the ADoQ domain.
We found 5,642 open resolvers seemingly resolving the ADoT domain. However, a closer look reveals that the great majority of those rely on Quad9 as their upstream resolver. Quad9 has actively promoted the ADoX deployment and recently enabled ADoT globally. We also observed resolvers operated by the Foundation of Applied Privacy, which acknowledged the experimental deployment of the draft predating RFC 9539.
Closing thoughts
Our measurements present a clear picture - ADoX deployment exists, but remains sparse and highly concentrated. Fewer than 1% of registered domains support RFC 9539, with a single operator (One.com) accounting for 2 million ADoX domains. Very few open resolvers support ADoT, and none resolved our ADoQ-only domain.
We hope this data-driven analysis helps guide DNS operators toward a pragmatic approach to improving privacy on the recursive-to-authoritative link.



Comments 0