The RPKI Browser is a graphical user interface to the objects of the distributed RPKI repository. The development is at very early stage. In this article, we ask for external input in terms of use cases, features etc.
Background
An RPKI repository consists of multiple objects, such as certificates, revocation lists, and Route Origin Authorisations (ROAs). There are several command line tools available to inspect these objects. However, there is only limited work that provides an intuitive graphical interface. The RPKI Browser implements a graphical interface to analyse the content of RPKI objects and their dependencies. The RPKI Browser is open source, and currently at a very early stage. To shape the development of this tool with the requirements of potential users in mind, we would like to ask for input from the operator community.
In this note, we briefly explain the current state of the RPKI Browser to kick off the discussion for use cases, features etc. Please, let us know what you expect from an RPKI Object Browser. Either leave your comments below or send an email to rpki-miro@googlegroups.com .
The RPKI Browser is available at http://rpki-browser.realmv6.org . We will publish the source code on Github as soon as a more mature version is ready.
RPKI Browser - Basic Functions
The RPKI Browser periodically fetches all RPKI data from a set of predefined trust anchors. At the moment, data from all five RIRs is hourly collected.
The current GUI consists mainly of two parts, the menu and the content view.
Menu
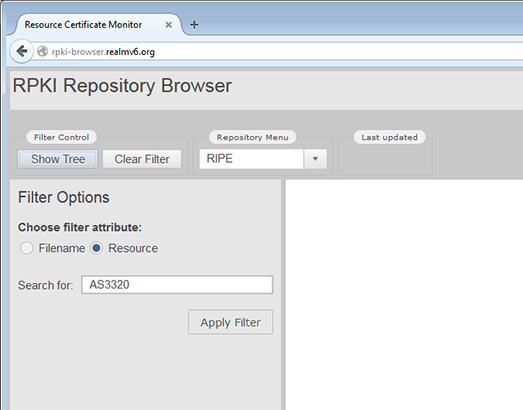
In the menu (shown below), you can select the repository that you want to inspect, and you can configure filters. Please note that filtering for AS numbers requires the prefix "AS" (e.g., AS3320).
Content View
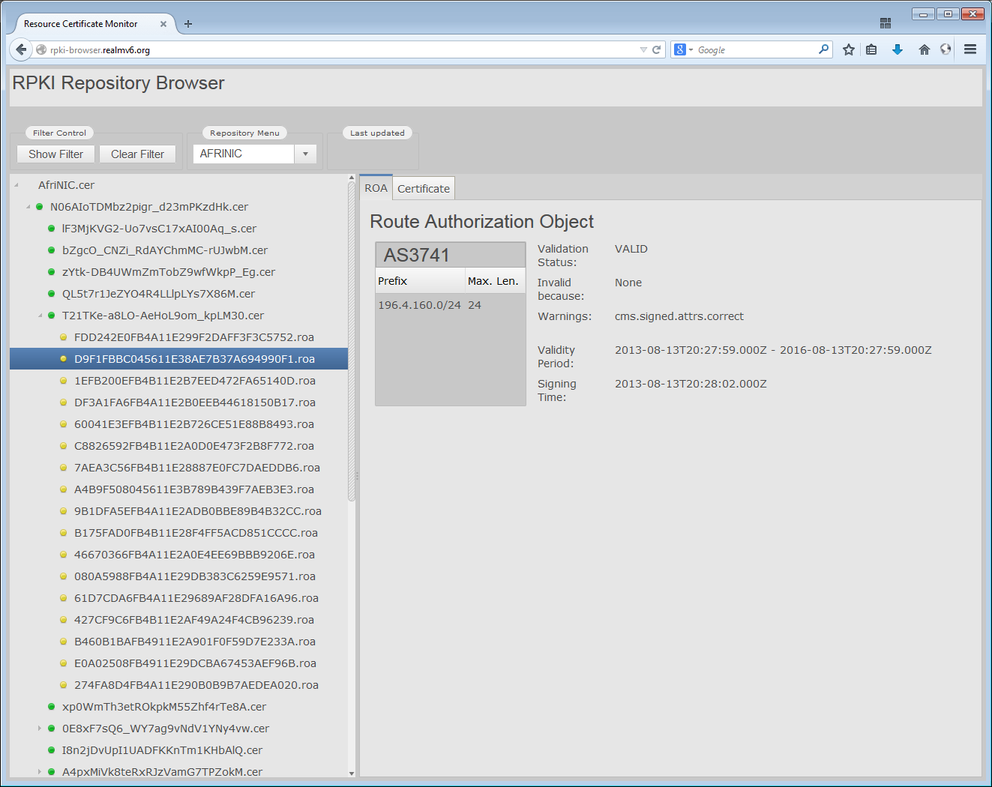
The column at the left hand side shows the RPKI object tree. Showing all possible objects would overload the view. We decided to include only certificates and ROAs. The root of the tree is the selected trust anchor.The colour of a node indicates the cryptographic validation state of the object, i.e., green = passed, yellow = warning, red = error.
The column at the right hand side shows the content of the selected object as well as related objects. For a certificate the corresponding manifest and certificate revocation list (CRL) are presented; for a ROA, the corresponding end-entity (EE) certificate is shown.
Screenshots (click on the images to get a larger view)
| Certificate Content | ROA Content | EE Certificate Content of Selected ROA |
Conclusion
We highly encourage you to participate in the development process of the RPKI Browser, even at early stage. The current set of functions is very limited and serves more as an illustration of the basic idea. Let us know your use cases and requirements for such a tool! Which features (e.g., additional views, download of object data) would you like to see implemented? Send an email to rpki-miro@googlegroups.com or leave your comments below.


Comments 0
The comments section is closed for articles published more than a year ago. If you'd like to inform us of any issues, please contact us.