As the Internet moves into the inevitable age of IPv6, new kinds of security challenges calling for new kinds of solutions await. In this article, we look at how our IPv6 security course is helping people and organisations get prepared to keep the future Internet secure.
IPv6 has been a long time coming. But now - with IPv4 exhaustion having become old news and global IPv6 penetration figures steadily rising - it looks like things are really getting somewhere. In fact, as IPv6 is said to be growing faster than IPv4, it’s only a matter of time before the new protocol becomes the more widely used.
All this is great news for the future growth of the Internet, but wider adoption of IPv6 has its consequences. One of the most important of these is the need for better IPv6 security, both for current networks and as a requirement for the implementation of new ones.
A New Flavour of Security Challenges
The importance of IPv6 security isn't hard to sell. More and more people are recognising the need to make the move to IPv6, and at the same time, concerns about Internet security remain high. Indeed, in the results of our most recent RIPE NCC Survey, we saw respondents calling for more practical information on IPv6 deployment while also citing network security as the biggest challenge faced by their organisations.
For a time, it wasn’t unusual to hear claims to the effect that IPv6 would do away with some, perhaps even many, Internet security issues. But while this might have made for a flashy headline or two, and maybe even pushed some to take more notice of IPv6, it’s a pretty well debunked myth by now.
IPv6 is no more and no less secure than IPv4. That said though, it is a different protocol with its own security considerations. And you have to design and implement your IPv6 network with those considerations in mind.
So, ok, there are many similarities with IPv4 because it‘s a network or layer 3 protocol and many principles are the same. And there are some security issues related with other layers of the Internet stack – e.g. the transport or application layers – that are not affected by the choice of IP version.
Still, as a new protocol, IPv6 brings with it a new flavour of security challenges and solutions. So as part of the work we do to help make sure the Internet is stable and will remain so into the future, here at the RIPE NCC, we offer a course explicitly designed to help people get prepared to deal with IPv6 security.
Where to Begin with IPv6 Security
Many network engineers are still warming up to IPv6, much less IPv6 security. So where do you begin?
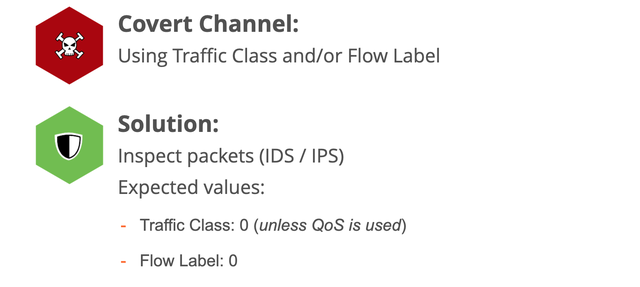
Well you need to begin with the basics of the IPv6 protocol. For example, you need to get an understanding of what extension headers (which are new to IPv6) do, and what kinds of attacks they are vulnerable to. Knowing and understanding how these can be used to bypass security filters means you'll pick tools that can properly deal with all combinations of extension headers.
Once you have the basics in place, you can then learn about other challenges that emerge with the move to IPv6. One of these, for example, is the use of Global Unicast Addresses (GUAs), equivalent to IPv4 public addresses, which tends to raise concerns for IPv4-minded engineers. Any IPv6 enabled interface will have - in addition to a link-local address, that allows for communications within the LAN/VLAN - a GUA. And indeed, having several GUAs is not an issue with IPv6, and is considered a feature of the protocol (for example to make it easy to renumber a network). However, this brings about security implications, as it's not so easy to control/monitor network activity of an IPv6 host.
And then there are security measures specific to the protocols used in IPv6 networks. For example, the Neighbour Discovery Protocol (NDP) and Multicast Listener Discovery (MLD) work on a link and can be used for different attacks that range from scanning for hosts to Man-in-the-middle (MITM) attacks. As you would expect, there are specific solutions and measures against these threats that are specific to IPv6, for example a set of techniques called First Hop Security (FHS) that are implemented on the switch.
Hands-on Experience
As a trainer who in pre-covid times was on the road for an average of around 60 days a year, by my calculations, I have trained close to 2,000 engineers face to face on a whole range of topics since joining the RIPE NCC in 2016. In that time, the kinds of questions that have come up about IPv6 security tend to be things like: Where do I start? What should I take into consideration? If I already have some knowledge about IPv4 security, what’s the new stuff that I need to find out? What’s changed? Can I reuse my knowledge?
As these questions around IPv6 security came up more and more for me and my colleagues over the years, and as the RIPE NCC Survey 2016 confirmed a strong need for more information both about IPv6 and about security, we realised that putting together a training course would be the best way to help people find answers on this important topic.
We've been teaching the RIPE NCC IPv6 Security Training Course for four years now, helping people pick up the basics of the IPv6 protocol – basic and extension headers, the addressing architecture, and so on – before moving on to the protocols used in IPv6 networks – ICMPv6, NDP, MLD, DNS and DHCPv6 -- then getting into broader considerations about Internet-wide security.
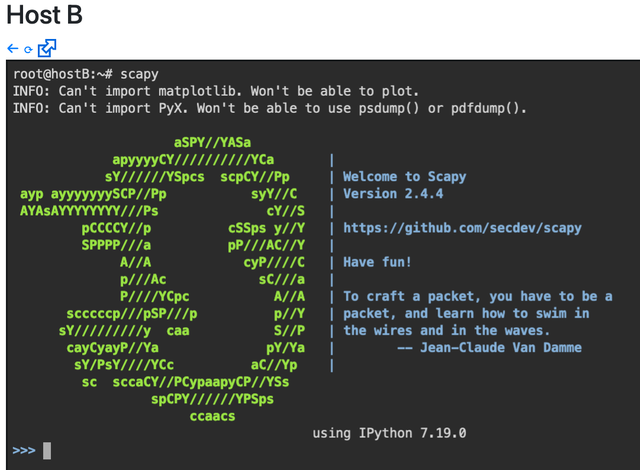
For me, and for many of those who completed the course, a big strength of the training we do in this area revolves around putting the relevant ideas into a practical context. We provide an environment in which participants can get hands-on experience trying out the different tools that they’ll later on use in the wild to secure their own networks, and we also share lots of tips about which devices are expected to support which security features, how you can find up to date information, and what other tools can be used to get on with the necessary tasks.
You can learn more about the RIPE NCC IPv6 Security Training Course on our website. While both the IPv6 security course and webinars are currently available to RIPE NCC members only, note that we'll be introducing the RIPE NCC Certified Professionals certification ‘IPv6 Security Expert’ and an e-learning version of the course in the very near future. Look out for more news on this on RIPE Labs!


Comments 0
The comments section is closed for articles published more than a year ago. If you'd like to inform us of any issues, please contact us.