As a part of the RIPE NCC's ongoing engagement with the Internet Exchange Points (IXPs) we have organised a code sprint. Researchers and IXP developers got together to continue work on the projects started during the IXP Tools hackathon, and achieved new, tangible results.
This article is a short summary of the achievements during the code sprint. Look out for detailed descriptions of all these projects in future RIPE Labs articles.
Introduction
The code sprint was held on
This event is one of the steps in our continuous engagement with IXPs. Previously, we had: the "IXP workshop" in Belgrade with ISOC; IXP-country-Jedi "release" and many presentations; the "IXP Tools" hackathon at RIPE 73; and the Euro-IX workshop in Krakow. Follow-up steps include: presenting the results RIPE 74 in Budapest; and at the SEE 6 Meeting in Budva.
As always, the coding session has been powered by coffee and stroopwafels.

Remote Peering Detection API
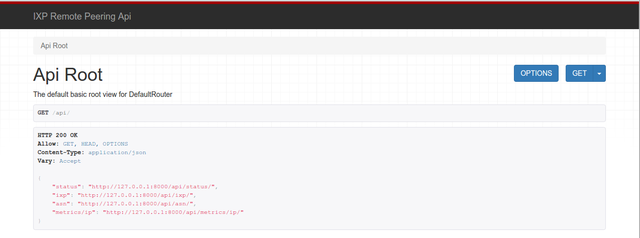
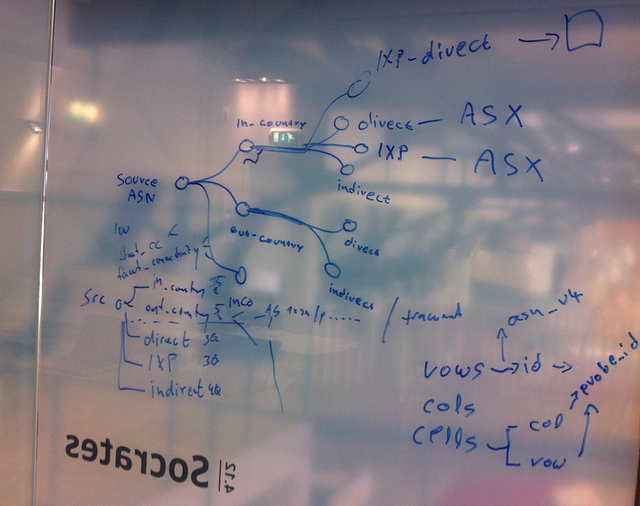
During the IXP Tools hackathon in Madrid, a tool for detecting remote peering was developed. You can access the working prototype at http://inspire.edu.gr/rp/. The goal for this code-sprint was to define an API so that access to the collected remote peering data can be standardised and automated, thus allowing other organisations to create visualisation tools (for example, RIPE NCC could add this to RIPEstat, or IXPs can add it to their user portals).
The team, consisting of Eleni Fragkiadaki (LINX), Matthias Hannig (ECIX) and Vasileios Giotsas (Caida) designed both he database data structure, and the several API calls, for various views: IXP view, ASN view, and a set of query parametres in the "metrics" API call.
The work continues remotely, while Vasileios is visiting the RIPE NCC offices as part of his award from the previous hackathon. The follow-ups will be the publication of scientific paper, an article for RIPE Labs, and more!
IXP Country Jedi Improvements
The default result of the IXP Country Jedi is a large matrix of all the ASNs in a country that have RIPE Atlas probes, with colour-coded values for paths going out of the country (or not), and paths going through an IXP (or not).
One feature requested long ago was to be able to see the results of the "country traceroute mesh" for a specific network (ASN).
During the code sprint, the team consisting of Petros Gkigkis (FORTH), Alex Milolidakis (FORTHt) and Emile Aben (RIPE NCC) came up with an elegant solution: display only the "interesting" information. On this approach, cases are only displayed if the traceroute path is going out of the country, and if there is no direct peering, which would mean there are intermediate networks between source and destination ASN.
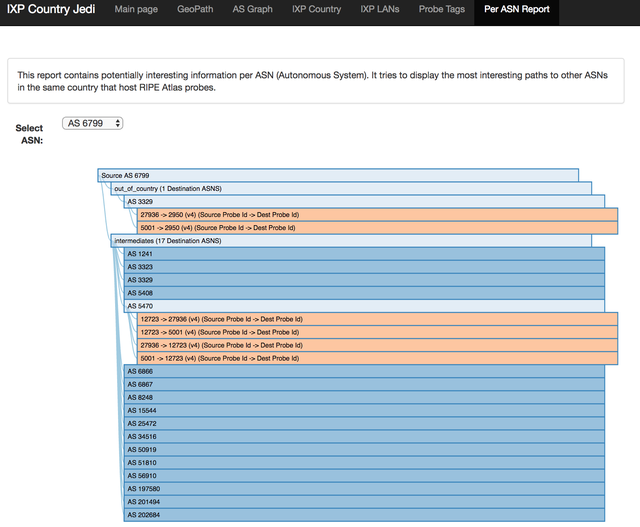
There is a "prototype of the prototype" available to try out, with the up-to-date data for Greece. The work continues, since Petros is visiting the RIPE NCC offices as part of his research internship.
BirdsEye LookingGlass
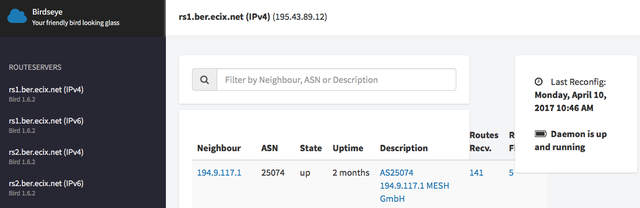
In addition to these two featured projects (which have seen progress during the code sprint), we learned from Mathijs that one more concrete follow-up has been made since the hackathon in Madrid: "BirdsEye" looking glass has been deployed at Ecix Internet Exchange in Berlin! You can do the lookup at lg.ecix.net.
Conclusions
Although small in scope, this event has brought great results. Two existing tools have been improved, new cooperations have been forged, and ideas for future cooperation have been born. Stay tuned for the updates on the details of the above mentioned projects!





Comments 2
The comments section is closed for articles published more than a year ago. If you'd like to inform us of any issues, please contact us.
Michael Oghia •
Hi Vesna, thanks for covering this! Does the Country Jedi have to be installed from GitHub to use? Or is there an online portal? I am not sure how to get it to work, but I want to share it with people (and encourage them to use it). I liked Mirjam's presentation at the CEE Peering Days, and I think it could be really useful. Feel free to ping me on another platform too.
Vesna Manojlovic •
Hi Michael, thanks for your interest! Yes, IXP-Country-Jedi is available both as an installed version, and as an "online portal" - however, it is still a prototype! You can find the latest data per country here: http://sg-pub.ripe.net/emile/ixp-country-jedi/latest/ For example, Serbia: http://sg-pub.ripe.net/emile/ixp-country-jedi/latest/RS/ The additional "Per AS report" is only available for Greece, for now: http://sg-pub.ripe.net/petros/ixpcountryjedi/2017-04-01/GR/perasn/index.html And the code on GitHub is here: https://github.com/emileaben/ixp-country-jedi I hope you have fun using it, and thanks for pointing people to our tools! Cheers, Vesna