SSHCure is an Intrusion Detection System for SSH, developed at the University of Twente. It allows analysing large amounts of flow data and is the first IDS capable of identifying actual compromises. Being deployed in various networks, ranging from small Web-hosting companies to nation-wide backbone networks, SSHCure has proven to be a stable system in high-speed networks.
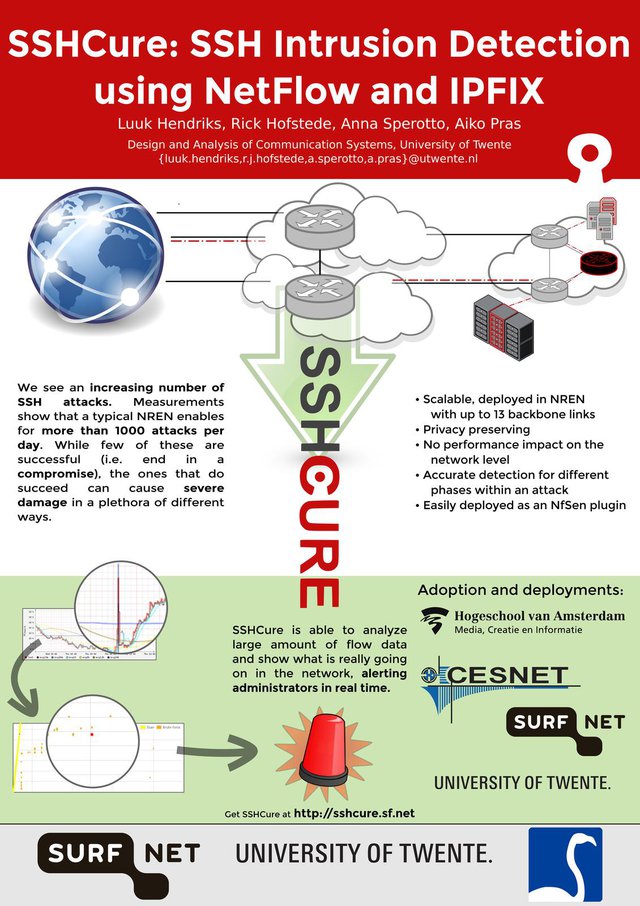
We see an increasing number of SSH attacks. Measurements show that a typical National Research and Education Network (NREN) receives over 700 attacks per day . While few of these are successful (i.e. end in a compromise ), the ones that do succeed can cause severe damage in many different ways.
SSHCure is the first SSH Intrusion Detection System that is capable of distinguishing successful from unsuccessful attacks, and thereby detecting actual compromises. As powerful as SSH is to administrators, as attractive it is to anyone with malicious intents.
Existing detection systems do not make such a distinction which makes it difficult for network administrators and incident response teams to filter out the few attacks that are successful. This can have severe consequences for the target hosts themselves, others hosts in the network, or even the network itself. Therefore, an NREN should be informed as quickly as possible when this happens, so adequate actions can be undertaken.
In SSHCure, we implement a detection algorithm based on flow export technologies , i.e. NetFlow and IPFIX . A flow-based approach has clear performance benefits over packet-based approaches in large-scale networks. The packet payloads are not available in flow data, making it more privacy preserving, while the loss of information (compared to packet-based approaches) is limited due to the encrypted nature of SSH. We show that flow data provides sufficient information to perform accurate detection. Moreover, flow export technologies are widely available on high-end networking devices. SSHCure is a plugin for NfSen (a popular flow collector for NetFlow and IPFIX), used by many in the networking community (and therefore easy to install and use).
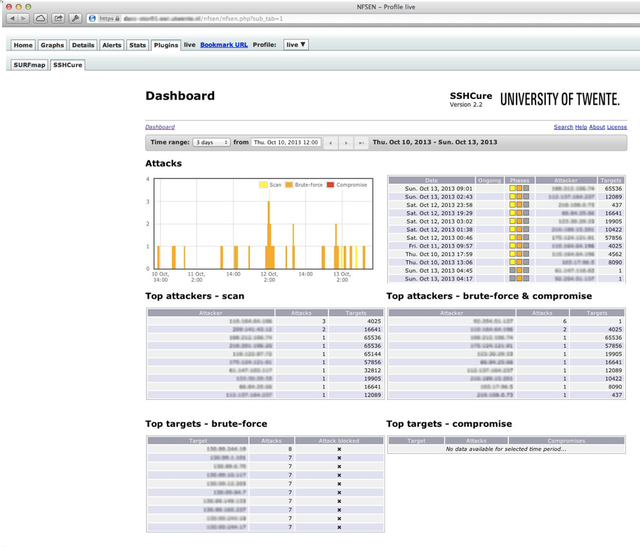
The adoption of SSHCure underlines this: it is currently deployed at several large commercial ISPs, CSIRTs/CERTs and NRENs. All of these types of organisations need to be able to act swiftly when a compromise has been observed. SSHCure is designed to support in that: the Web-interface (see the exemplary screenshot below) offers clear insight into the situation, including detailed information on both attacker and targets, comprehensible visualisations of networks, and raw flow data for extensive analysis if needed.
This is backed up by an extensible notification system, and (currently under development) integration with incident reporting systems via standard protocols (e.g. IODEF or X-ARF). SSHCure, available via Sourceforge , has been in development for 2.5 years, and is still actively being developed and supported. The first prototype was presented at the Autonomous Infrastructure, Management and Security conference (AIMS) in 2012, and promising results were achieved. With the latest available version, we performed extensive validation using data sets from both campus and backbone networks. Results show detection rates up to 100%.
This project was recently presented at the TERENA Networking Conference ( TNC 2014 ) where we expand our audience and explained how NRENs can benefit from SSHCure in their operations. The poster below was presented at TNC 2014. The work on SSHCure is partly funded by FLAMINGO , a Network of Excellence project (ICT-318488) supported by the European Commission under its Seventh Framework Programme.
Are you SSHCure?
Using the provided installer, SSHCure is easily deployed in a matter of minutes. Try out SSHCure now, at let us know what you think about it. For any form of support, feature requests or to receive updates on development, please consider subscribing to our mailing list .
As of this week, SSHCure's latest version 2.4b2 is available for download .




Comments 2
The comments section is closed for articles published more than a year ago. If you'd like to inform us of any issues, please contact us.
fx •
The link to the mailing list seems to be broken
Luuk Hendriks •
My best guess is that's related to the current problems at SourceForge, I can't access the project page either.