Routing loops can trap packets between routers, preventing them from reaching their destination. In some cases, routers even duplicate looping packets, amplifying traffic and threatening Internet stability. We look at how this happens and how operators can prevent it.
Routing loops cause packets to circulate between routers instead of being delivered. In some cases, these routers duplicate each looping packet over and over again amplifying the resulting load exponentially. This unnecessary traffic can congest links, overwhelm routers, slow routing convergence, enable DoS attacks, and ultimately reduce the stability and reliability of the Internet.
In a recent measurement study, we found that, despite being easy to fix, routing loops and amplification of looping packets are fairly common. This suggests that the network operator community is not prioritising these issues. In this blog post, we want to draw attention to the impact of routing loops and amplification of looping packets so that these misconfigurations are hopefully solved in the future.
Providers often hand out large chunks of so-called provider-aggregatable (PA) address space to their customers. Those customers often use only a small fraction of assigned IPv6 address space, which can lead to routing loops if not properly configured. A serious bug in the firmware from common router vendors that is triggered by routing loops can lead to significant amplification. Unlike IPv4, this problem is more prevalent in IPv6 since the IPv6 address space is sparsely populated.
Routing loops are unnecessary and should be fixed! You can check whether your network is affected on https://ipv6-sra.realmv6.org/routingloops.
What causes routing loops?
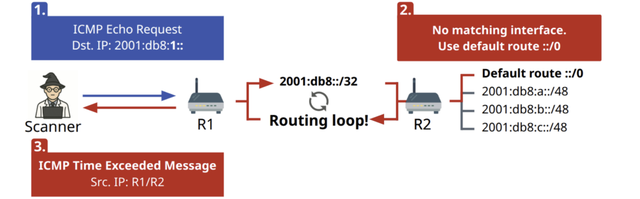
Internet routing loops often occur when the following two configurations collide.
- A provider maintains a downstream route to its customer. The customer, however, uses only some more specific prefixes of the covering route maintained by the provider. This covering downstream route makes both the used and unused address space reachable via the upstream of the customer.
- The customer also maintains a default route to the provider, packets to the unused address space are then sent back to the provider since the customer does not have any more specific route than the default route. Consequently, packets to the unused address space are sent back and forth between customer and provider until the hop limit is exceeded.
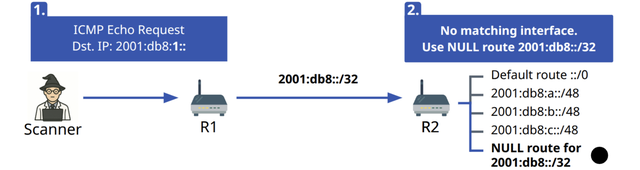
How to prevent routing loops?
To prevent routing loops triggered by downstream peers of the customer, the customer router needs to drop packets destined to the unused address space.
In many router implementations, this is achieved by using null routes.
For example, a customer that has been assigned the prefix 2001:db8::/32 but only uses the parts 2001:db8::/34 and 2001:db8:8000::/34 must exclude traffic to 2001:db8:4000::/34 and 2001:db8:c000::/34 from further forwarding.
Instead of configuring each null routed prefix separately, many router configurations allow configuring a null route using a single line. At some Cisco and Juniper routers it may look like the following:
Cisco IOS: ipv6 route 2001:db8::/32 Null0
Juniper Junos OS: set aggregate route 2001:db8::/32
These configurations instruct the router to drop traffic to 2001:db8::/32 if no more specific route is available.
Amplification bug in the firmware from common router vendors
During our active scans, we discovered a serious bug in the firmware from common router vendors that is triggered by routing loops, and can lead to significant amplification. A single ICMPv6 Echo request can result in more than 250,000 replies from the same router. We confirmed our observations with network operators, and router vendors. Routing loops, in conjunction with the amplification bug, can be exploited for denial-of-service attacks, posing a significant risk to network security.
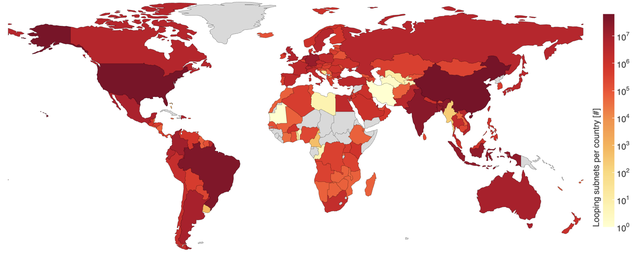
Global deployment of routing loops
We observed routing loops triggered by 419M /64 subnets. These subnets affect 7.1M IPv6 router addresses, distributed in over 163 economies.
Most IPv6 routers involved in loops only have one misconfigured /64 subnet. But a tiny number of routers are responsible for an enormous number - over a million each - of broken /64 networks, making them disproportionately responsible for routing loops on the IPv6 Internet.
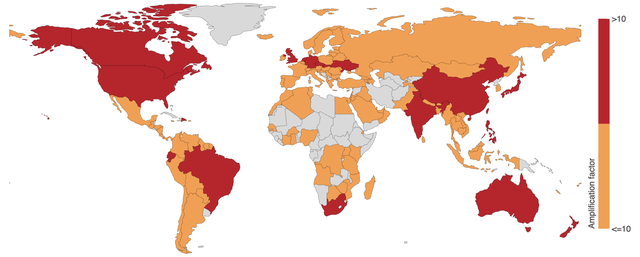
Global deployment of the amplification bug
Of the 7.1M IPv6 router addresses affected by routing loops, 34k are also affected by amplification. These IPv6 router addresses are highly concentrated in Brazil (28%), India (19%), and China (16%).
While 87% of the amplification factors are below ten, a few routers amplify single ICMP Echo requests exponentially, significantly increasing the threat potential of these devices. These routers are primarily located in Brazil (80%) and China (17%). The highest amplification factors can be observed in Germany and Japan.
Two mitigation steps for network operators
- Check if your networks are affected: We publish our measurement results and provide a form to check if your network is affected by routing loops here.
- To prevent routing loops, it is advised to set NULL routes for all unused subnets of the assigned address space, if you deploy default routes.
More details are available in our publication ‘Scanning the IPv6 Internet Using Subnet-Router Anycast Probing’ presented at ACM CoNEXT 2025 and published in the Proceedings of the ACM on Networking Vol. 3, No. CoNEXT4, 2025.


Comments 0