Last time, we looked at legacy address space in terms of contract coverage, ROA coverage, and proportion of announced prefixes. Now it’s time to take a closer look at those blocks still to be brought under contract and get a clearer picture of what kind of behaviour we see coming from them.
Two years ago, we wrote an update on the legacy policy a decade in. We looked at the history of legacy, the policy itself, and what motivated it. We also showed how much of the legacy address space administered by the RIPE NCC had been brought under contract, how much was being announced, and how much was covered by RPKI.
The bottom line was: efforts to make legacy holders aware of their options for registering resources in the RIPE Database saw the share of legacy resources under contract rise from 4% to 72% between 2014 and 2024. But despite some big jumps along the way, gains had been slow and steady for the most part. By January of this year, the numbers had only risen a further 4%.
So why the focus on bringing legacy under contract? Well, maintaining a clear formal relationship with legacy holders helps keep their registry data accurate and their status as resource holders better protected. It helps make sure holders stay in contact with - and contribute to - the RIR ecosystem. And, moreover, bringing resources under contract is necessary for using RPKI, which helps protect resources against routing hijacks.
When that relationship is missing, these advantages are reduced. Without the formality and protections that come with a contractual relationship, it’s easy to think of out-of-contract legacy as somehow unchecked and unruly - a kind of wild west of the IPv4 address space. But is that a fair picture? And is it a useful one for future conversations around legacy?
Here we take a first step towards answering these questions. Focusing on out-of-contract legacy, we ask how the prefixes appear in global routing over time, whether they’re reachable, and whether there’s evidence they have been put to bad use. The picture that emerges isn’t uniform. Some parts of this space appear stable and reachable, others less so, while some appear to be dormant. Our aim is not to evaluate the current state of affairs, but to provide a clear overview of how and where these different parts overlap. We hope this will aid future discussion and analysis of legacy resources and their role in today’s Internet.
Legacy today
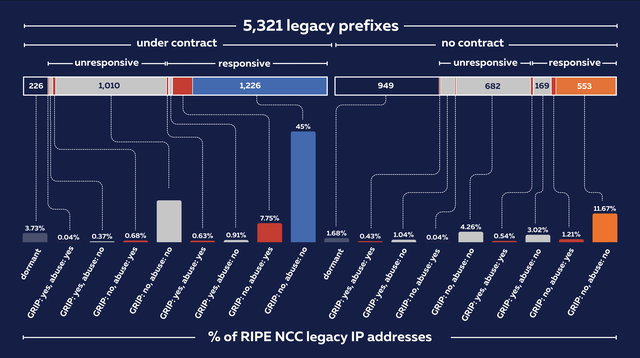
The figure below provides a January 2026 snapshot of legacy in terms of contract coverage, announcement status, and ROA coverage.1 We highlight legacy in the context of the wider RIPE NCC IPv4 pool (left), then show how much of that is still without contract (right).
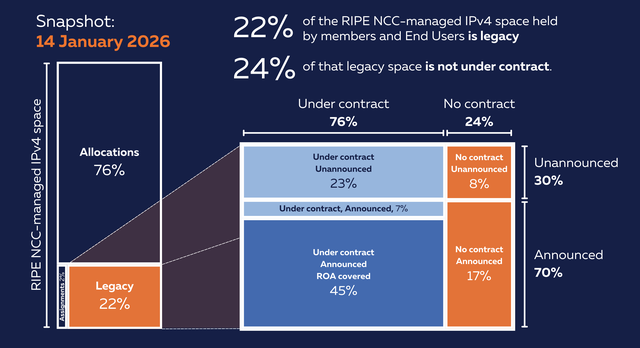
Comparing this to what we saw two years ago, the amount of legacy covered by ROAs has gone up a little - from 41% to 45% - while legacy being announced is at 70%, up from 61%.
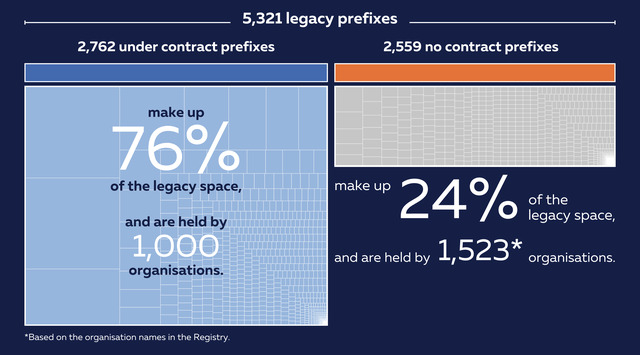
The ‘no contract’ bin makes up 24% of the space on show. That’s around 44 million addresses across 2,559 prefixes held by approximately 1,500 organisations.
One point worth noting here is that all the ‘bigger’ legacy holdings - from the /14s up to the really big /8s - have already been brought under contract. The rest, our focus here, is made up of smaller blocks (mostly /24s, though the bulk of IP space here is made up of /16s).
Legacy behaviour
What kind of behaviour do we see coming from out-of-contract legacy resources? To answer, we look at three different dimensions of activity: visibility in routing; reachability; and anomalies and abuse behaviour.
1. Routing visibility over time
Let’s start by expanding on the snapshot above to see how our target prefixes appear in BGP routing history from January 1999 to October 2025. Note that all our BGP data comes from RIPE RIS.
One immediate challenge is that prefixes can appear in historical routing data for reasons that do not necessarily reflect meaningful or sustained operational use. Routing artefacts, aggregation effects, and short-lived announcements can all inflate apparent visibility. For example, in BGP, networks commonly advertise aggregated routes that cover multiple more-specific prefixes, so smaller prefixes can appear within larger (less specific) announcements. As a result, when we look for our target prefixes in the raw routing data, we observe 934,852 announcement intervals (continuous periods during which a prefix is visible in BGP) spanning 16,482 distinct routed prefixes.
To avoid overstating visibility, we apply a conservative filtering method to remove certain known sources of inflated visibility. These filters are applied sequentially, with each step operating on the output of the last:
- Coarse prefix announcements: Extremely large routing announcements (less specific than a /8) can dominate the routing table while providing little insight into the intentional routing of legacy prefixes. Default routes (
0.0.0.0/0) and similar announcements - often the result of route leaks or misconfigurations - are therefore removed. Removes 55,309 intervals, 74 prefixes (2.89%), covering 2 million legacy addresses (4.56%). - Global visibility threshold: We require evidence of global reachability by filtering out announcements observed by fewer than 10 RIS peers. Prefixes with such limited visibility are typically localised or weakly propagated and do not meet the criteria for global routing visibility used in this study. Removes 35,017 intervals, 22 prefixes (0.89%), covering around 400,000 addresses (1%).
- Temporal stability: To distinguish persistent routing behaviour from ephemeral noise, we retain only [origin ASN, prefix] combinations visible for a cumulative duration of at least 15 days over the 16-year period. This is a deliberately permissive definition of persistence, again to avoid over-filtering. Removes 853 prefixes (34.63%), covering 685,000 addresses (1.5%) (removed announcements average 12 days of visibility, compared to 1,793 days for those retained).
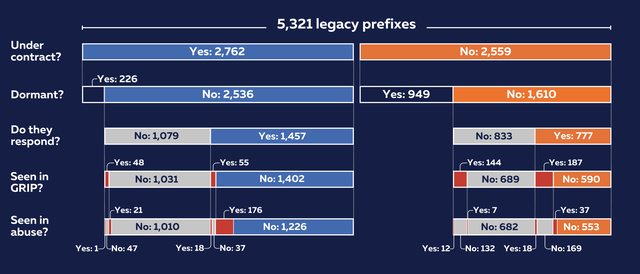
In total, filtering eliminated 949 prefixes. That’s around 3.1 million IPv4 addresses (or 7% of out-of-contract legacy space) for which we find no strong evidence of sustained, globally visible routing activity. Based on RIS data, a meaningful portion of out-of-contract legacy space appears to have been dormant over the observed period.
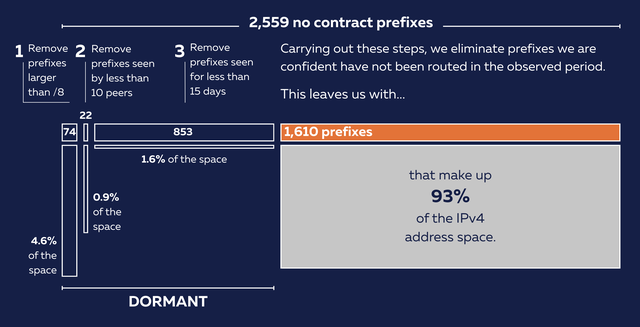
The remaining 1,610 prefixes pass our visibility criteria. Even then, routing visibility alone doesn’t imply active use. Some blocks may remain visible due to aggregation, defensive routing, or other non-deployment patterns. Given that our thresholds (e.g. ten peers, fifteen days) favour retention, these results should be interpreted as a lower bound on dormant space, identifying only cases where lack of visibility is unambiguous.
A couple of quick notes before we move on. First, the removed prefixes are smaller: 85% are /24s, compared to the routed group where 34% are /16s (and the median prefix is a /22). Smaller legacy allocations seem to be more likely to have remained dormant (perhaps, in some cases, they became dormant early on when organisations, looking for more space in the growing Internet, renumbered into bigger allocations). Second, lack of visibility in global routing data does not necessarily rule out internal or private use.
Third, we also observe 226 dormant prefixes in legacy under contract. This actually accounts for 3.73% of the total legacy address space administered by the RIPE NCC, compared to 1.68% for dormant out-of-contract legacy space (see summary at end of article). When we compare out-of-contract and under-contract legacy below, note that we’ll generally ignore dormant prefixes on both sides.
2. Reachability and usage
Although some degree of consistent visibility in the global BGP routing tables over time can help rule out dormancy, it doesn’t tell us much about operational deployment or active use. To build a more nuanced picture of behaviour, we next look at reachability and usage patterns for the 1,610 out-of-contract prefixes left over after filtering.
Network-layer reachability
We examined ping response data from the Analysis of Network Traffic (ANT) Internet Address Census (dataset it111w, collected February-March 2025), which swept all IANA-allocated IPv4 addresses with a single ICMP echo request per address. We extracted results for all 1,610 legacy resource allocations to determine what fraction of this space responds to network-layer probes.
Of the 41 million out-of-contract addresses measured, only 805,364 addresses (1.97%) responded to ping requests. However, the distribution of responses was highly uneven across prefixes: while 777 (48%) contained at least some responsive addresses, 833 (52%) contained none at all. Those latter prefixes represent 26% of total legacy space, meaning nearly one-quarter of addresses we tested show no network-layer activity detectable over ICMP. This doesn’t altogether rule out reachability - networks can be configured not to respond to ICMP echo requests - but the absence of responses across entire prefixes may be a noteworthy signal when considered alongside other indicators of activity.
For comparison, 57% of under-contract legacy prefixes show some level of ICMP responsiveness, compared to 48% of out-of-contract prefixes. However, when weighted by address space rather than prefix count, this difference almost disappears: 74% of out-of-contract space sits behind responsive prefixes, compared to 75% for under-contract legacy. This suggests that much of the difference is concentrated in smaller allocations, while larger allocations behave similarly regardless of contract status.
Note that only 105 prefixes (6.52%) exhibited response rates exceeding 10%, with the median response rate across all prefixes at 0%. The dormant prefixes identified in the previous section show no ICMP responses whatsoever - none of the 949 prefixes produced a single responding address. This independently corroborates the dormancy classification: prefixes that showed no sustained BGP visibility also show no network-layer activity.
Application-layer usage
To assess whether legacy space with stable routing visibility hosts real Internet services, we analysed domain-to-IP mappings from the Chrome User Experience Report (CrUX) for our 1,610 prefixes. We obtained the CrUX top 1 million domains, resolved their DNS A records, and identified which domains map to IP addresses within these filtered legacy CIDR blocks.
According to the results, 4,759 domains from the CrUX top 1 million are hosted on out-of-contract legacy address space, including: 1 domain in the top 1,000; 19 in the top 10,000; and 150 in the top 50,000. These domains resolve to 3,560 unique IP addresses distributed across 238 distinct legacy CIDR blocks. Conversely, only 14.8% of the filtered legacy prefixes (238 out of 1,610) host any domain from the top 1 million, while just 38 prefixes host domains ranked in the top 50,000.
From visibility to active use
Taken together, these measurements establish a funnel from routing visibility to operational deployment. Among the 1,610 legacy prefixes that passed our filters, only 777 (48%) show any network-layer reachability via ICMP, and just 238 (15%) host popular web domains. Even among consistently routed prefixes, over half show no responding hosts, and fewer than one in five host widely used web services. A large portion of out-of-contract legacy space may still be routed, but shows little evidence of active Internet deployment.
Viewed at the ASN level, this pattern becomes clearer. Although out-of-contract legacy resources represent only 1% of IPv4 address space, they are distributed across 464 origin ASNs, 71% of which announce just a single prefix. Usage, however, is far more concentrated: 85% of visible prefixes host no popular domains, while a small subset supports nearly 5,000 domains, including sites in the top 10,000.
3. Anomalies, misconfigurations, abuse
So far we’ve been concerned with the question of whether we see activity coming out of legacy prefixes. We now look at what kind of behaviour we see when we do.
Routing anomalies and misconfigurations
To assess the routing stability and security posture of the 1,610 legacy resources that passed our visibility filters, we analysed BGP anomaly data from GRIP (a system that detects and classifies BGP hijacks and routing anomalies) covering the past five years. This independent dataset provides insight into potential misconfigurations and BGP incidents affecting legacy space that appears stable by basic visibility metrics.
GRIP detected 1,899 unique routing anomaly events involving 331 of our out-of-contract prefixes (98 show up in medium-severity events, and 169 in critical events). 204 of these events (4.8%) were classified as explicit misconfigurations. The dominant event type was MOAS (Multiple Origin AS) announcements, accounting for 89% of all events, with SubMOAS events comprising the remaining 11%.
Are these numbers high? To get a feel for this, we performed the same analysis on the 2,536 non-dormant legacy prefixes under contract (remember: 59% of this space is covered by ROAs according to our opening snapshot). The contrast is quite striking: only 4.1% of under-contract prefixes appeared in GRIP events, compared to 20.6% of the no-contract prefixes - a five-fold difference. Similarly for critical-severity events: 10.5% of no-contract prefixes appear in critical incidents versus just 2.6% of under-contract prefixes (four-fold difference).
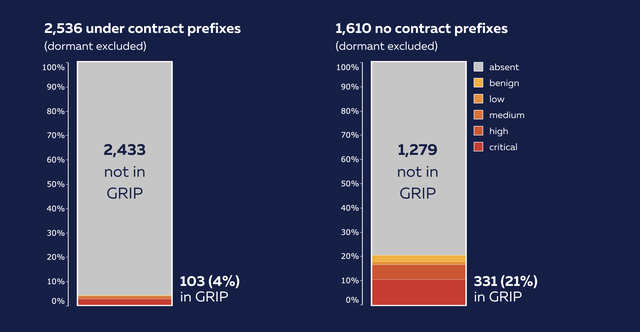
These results indicate a clear correlation between contractual status and exposure to routing anomalies. While multiple factors may contribute to this difference, the ability to deploy RPKI and maintain up-to-date registry information likely plays an important role in reducing operational and security risks.
Threat intelligence signals
The routing anomaly data above shows how often out-of-contract legacy space appears in BGP incidents. But what do external threat intelligence feeds tell us about what is actually originating from this space?
Address space associated with abuse activity tends to be filtered, blocked, or de-preferred by operators. These consequences apply regardless of who is responsible, affecting both legitimate holders and the wider routing ecosystem. We cross-referenced the 1,610 actively routed out-of-contract prefixes against five widely used threat intelligence feeds (Blocklist.de, IPsum, FireHOL Level 1, URLhaus, and Spamhaus DROP; see note 2), each capturing a different dimension of abuse activity. This provides a point-in-time snapshot of how this space is represented in operational security datasets.
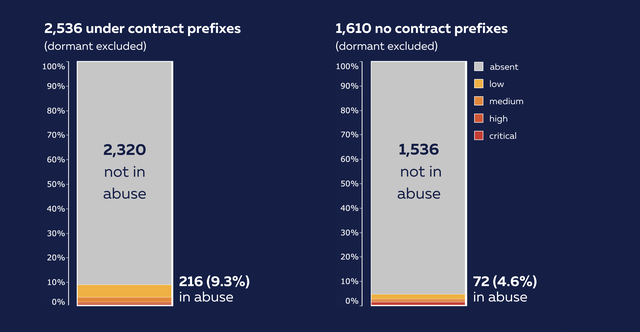
Across these prefixes, 74 (4.6%) were flagged by at least one feed, corresponding to 775 unique IP addresses. As before, the distribution is uneven. In the blocklist.de dataset, a single prefix accounts for nearly 86.7% of all reported attack activity - a highly concentrated but weak signal, appearing in only one additional feed and with low confidence.
Stronger signals are rarer. Five were flagged by three or more feeds and 34 by exactly two, though given the partial overlap between feed sources, co-occurrence does not always represent independent corroboration. The remaining 35 prefixes appear in only one source, often with low confidence scores. URLhaus identified a small number of prefixes associated with malware distribution, including several actively serving malicious content at the time of measurement - concrete examples of live abuse infrastructure, though limited in scope.
The most significant signal comes from Spamhaus DROP. Unlike behavioural feeds, DROP designates entire network ranges as hijacked or under criminal control. We identified 17 prefixes - around 1% of the routed no-contract space - that fall entirely within DROP-listed ranges. Most are large legacy allocations (/16s), meaning a substantial volume of address space is associated with networks classified as wholly compromised. This signal is not independently corroborated by other feeds, but reflects a fundamentally different, network-level assessment.
These findings should be interpreted with care. The feeds reflect observed behaviour or external assessments, not ownership or intent. Abuse can occur without the knowledge of the registered holder, and in some cases the holder may no longer exist.
For context, we repeated the analysis for legacy prefixes under contract using the same feeds. Across most behavioural feeds, under-contract space shows higher rates of flagged activity even when normalised by prefix count: 8.52% of under-contract prefixes were flagged by at least one feed, compared to 4.6% of out-of-contract prefixes. These differences do not point clearly in one direction and may reflect greater deployment or better feed coverage.
Where the picture diverges most clearly is in the Spamhaus DROP data. Only 0.12% of under-contract prefixes fall within DROP-listed ranges, compared to 1.06% of out-of-contract prefixes - a roughly ninefold difference. Unlike behavioural feeds, DROP reflects a network-level assessment, so this gap is less easily explained by differences in deployment or visibility alone.
Taken together, these results suggest out-of-contract legacy space is not uniformly associated with higher levels of observable abuse. However, it is more likely to appear inside network ranges that the security community considers wholly compromised. Whether this reflects a causal relationship, shared underlying conditions, or the long-term effects of limited oversight remains an open question.
Summary
Let’s take stock of some of the findings we’ve arrived at:
- A meaningful portion of out-of-contract legacy space appears dormant. After filtering routing data, around 37% of out-of-contract prefixes (covering 7% of out-of-contract legacy space) show no strong evidence of sustained, globally visible routing activity, suggesting that a non-trivial share of this space may simply remain unused.
- Much of routed out-of-contract legacy space shows limited evidence of active deployment. Even for prefixes that appear consistently in global routing tables, only about half show any network-layer reachability, and fewer than one in five host popular web domains. Much of this space may be routed but shows limited evidence of active use.
- Out-of-contract legacy space appears somewhat less active - but not dramatically so. While a smaller share of out-of-contract prefixes show network-layer responsiveness compared to those under contract, the difference is modest. This suggests that, at a basic level of reachability, the two groups are not fundamentally different, even if other indicators diverge more clearly.
- Out-of-contract legacy prefixes appear more frequently in routing anomalies. Compared with legacy prefixes under contract, out-of-contract resources show a significantly higher presence in GRIP-detected routing events. While multiple factors may contribute, the lack of access to RPKI protection and less reliable registry data likely play an important role.
- At the same time, a significant subset appears stable and operational. Many out-of-contract legacy prefixes show long-term routing visibility, measurable reachability, and in some cases host widely used services. This underlines that this space includes both inactive resources and actively used infrastructure.
Here's a visual breakdown of how these findings fit within the broader backdrop of legacy address space administered by the RIPE NCC:
And here's a view showing what percentage of address space sits under the categories we end up with in the above:
What next?
As we signalled at the top of the article, the picture that emerges from this analysis is not a uniform one. Some out-of-contract legacy space appears dormant, some shows limited signs of use, and a smaller subset clearly supports stable and sometimes important Internet services.
Much of this reflects the fact that this address space was distributed at a time when allocations were often informal and not tied to the kinds of contractual or documentation frameworks we rely on today. Since then, organisations have changed, meaning that in some cases, contacts have been lost and records have become incomplete. As a result, we see everything from actively used networks lacking the documentation needed to enter into contract to prefixes for which no meaningful activity can be observed.
These differences matter because they have real operational impact. For instance, since out-of-contract legacy resources are more difficult to validate and protect, they could, as a result, be more likely to be treated with caution by network operators - for example, being filtered or deprioritised in routing decisions. This affects not only potentially dormant space, but also legitimate (and sometimes important) services running on legacy resources.
Any discussion about what comes next therefore needs to take this uneven landscape into account. At one end, the continued operation of stable services suggests that changes need to be handled carefully to avoid unintended disruption. At the other, the presence of apparently unused space raises questions about whether parts of the legacy pool ought to be returned to use.
One practical step already under discussion in the RIPE community is to improve the quality and transparency of registry information for legacy resources without contracts by verifying holder information and making this visible in the RIPE Database. While this would not resolve all questions around legacy policy, it could reduce uncertainty, support more informed operational decisions, and provide a clearer basis for further work.
The aim of this analysis has been to move beyond assumptions and provide a more grounded view of how out-of-contract legacy space is actually used today. What happens next will depend on how the community weighs these findings and decides to address a part of the address space that still reflects the Internet’s earliest history.
Notes
1. In April 2026, after the data used for this analysis was collected, a number of legacy IPv4 addresses were converted from LEGACY to ALLOCATED in the RIPE Registry. As a result, legacy space currently makes up about 20.6% of all IPv4 space managed by the RIPE NCC.
2. We cross-referenced prefixes against five widely used threat intelligence feeds, each capturing a different aspect of network abuse. These feeds provide complementary views but are not fully independent and should be interpreted accordingly:
- Blocklist.de: A community-driven reporting system where operators submit IP addresses observed attacking services such as SSH, mail, FTP, and web servers. It reflects near real-time observations of active attack behaviour.
- IPsum: An aggregated dataset combining signals from more than 30 public blocklists. Each IP address is assigned a consensus score, with higher scores indicating stronger agreement across sources and lower likelihood of false positives.
- FireHOL Level 1: A composite blocklist designed for broad deployment with minimal false positives. It incorporates several upstream sources, including Spamhaus DROP and various malware and command-and-control lists.
- URLhaus: Operated by abuse.ch and Spamhaus, this platform tracks URLs used for malware distribution and records whether they are active at the time of observation.
- Spamhaus DROP: A high-confidence advisory list of entire network ranges assessed as hijacked or operated by cybercrime infrastructure. Unlike behavioural feeds, DROP operates at the network level rather than the level of individual IP addresses and is designed to minimise false positives.
These feeds are not fully independent. For example, FireHOL incorporates DROP, and IPsum aggregates sources such as blocklist.de. As a result, co-occurrence across feeds may reflect shared underlying data rather than independent corroboration.





Comments 0