In July 2010 we looked at the effects of BGP route origin validation on mis-announcements and hijackings. In the meantime, we did some research based on comments and questions received by the community. The findings are described in this follow-up article.
Back in July, a brief study into the effects of BGP route origin validation on mis-announcements and hijackings was published on RIPE Labs.
When we presented this study at the APNIC 30 meeting last month, we received a number of questions that required some more research. See below a response to those questions.
1. How does the IPv6 Internet compare to IPv4, with respect to this type of BGP hijacking?
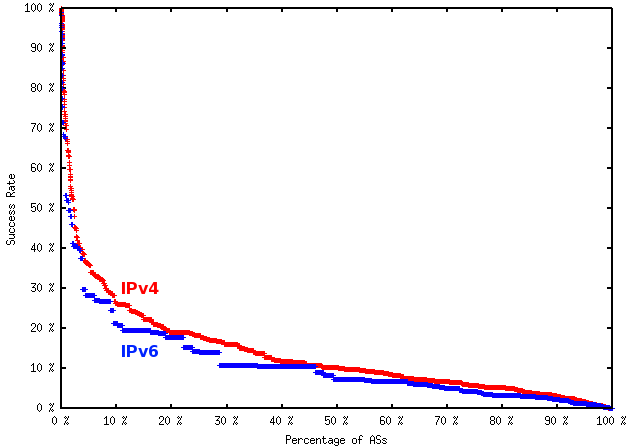
Based on the Routing Information Service (RIS) data, it appears that the (predicted) success rate for this type of hijacking is lower with IPv6 than IPv4. The mean success rate using IPv6 is 11.64% , compared with 13.63% with IPv4. This could be due to the increased connectedness (number of adjacencies) in the IPv6 Internet.
However, as the IPv6 data set is much smaller than the IPv4 data set, this may not be a fair comparison. The RIPE NCC is looking for more IPv6 peers to improve this data set in RIS. If you are interested in peering, please contact us .
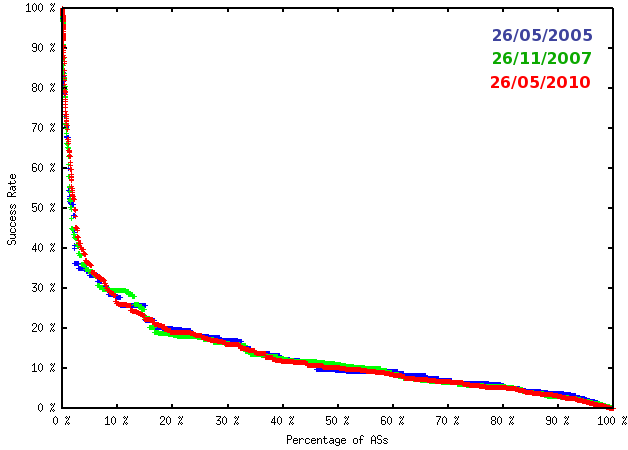
2. How have these results changed over time?
Historical RIS data can be used to estimate the variation in hijacking success over time:
| Date | Mean Success Rate |
|---|---|
| 26/05/2005 | 13.88% |
| 26/11/2007 | 13.69% |
| 26/05/2010 | 13.63% |
Little variation is seen over this period. This is to be expected, given how heavily these results are tied to AS path lengths. Although the Internet has grown substantially over the years, its diameter - the average AS path length - has remained at a surprisingly constant 3.8 hops.


Comments 1
The comments section is closed for articles published more than a year ago. If you'd like to inform us of any issues, please contact us.
Anonymous •
Do I understand correctly, that the increased robustness of IPv6 against hijacking is based on two simple facts:<br /> 1) only a few ISP do have IPv6 in production<br /> 2) IPv6 peerings are not that tightly conrolled by laywers<br /><br />So we get a better meshed network for IPv6 and can claim loudly "IPv6 is more secure than the old legacy crap".<br /><br />Fine. Thank you.