In this article we explain why we will be using Zoom for the upcoming RIPE 80 and RIPE NCC General Meeting, and we outline the policies and settings we have in place to address concerns about privacy and security.
Zoom comes from a different culture from ours! At RIPE and subsequently at the RIPE NCC, a pragmatic, lightweight and minimalist culture is dominant. Having openness and transparency in our DNA, the use of open-sourced technologies and solutions and openly standardised protocols is our natural choice. Zoom is none of those things! Zoom is closed-sourced and although it supports open standards and is built on top of many of them, it doesn’t use openly accessible technologies or protocols. I can bet the original Zoom design never had the RIPE community or Open Source folks in mind. Yet, we are going to use Zoom for the RIPE Meeting. Talk about diversity and acceptance, which is also in our DNA.
Zoom is a typical enterprise tool. The strange permission issue and webcam setup, which was unearthed last July, is actually not such a big surprise if you consider how many enterprise applications are developed and managed. Their “end-to-end” encryption is typical of promises in mid-sized enterprise applications, encrypting some data in transit and calling it end-to-end. But at the same time, they have found the sweet spot of usability and reliability and have created a service that users can interact with easily and is also generally reliable. There is not much competition for that spot - at least not yet. That is why we have selected Zoom as the main tool to run RIPE 80. We have tested multiple tools and platforms and have been in contact with other meeting organisers in our industry to get feedback on their experience. In the end Zoom, with all of its flaws, was a clear winner. Security is never perfect and one has to find the right balance between maintaining security requirements vs. other features.
At a high-level, it is possible to categorise Zoom vulnerabilities in three almost distinct categories:
- Meeting Security and privacy, referring to who can join, participate and interact at meetings and what happens to the data shared during the meeting via different channels (i.e. audio, video, file and screensharing and chat).
- User Security, referring to the effects of installing and having the Zoom application on end-user devices and possible security consequences it might have for the user.
- User Privacy, referring to whom users' data are shared with, who can control their microphones or webcams, and what data is being tracked and recorded for users.
These are critical factors for us. We never want to mandate the use of any tool that threatens the privacy or security of the RIPE community and RIPE NCC members or staff, so they can interact, meet, make decisions and policies and get work done. We want to facilitate a platform where all of these can be achieved with minimum risk and maximum freedom for each individual. Given that, any organisation should be conscious about the tooling they choose and the trade-offs they make. We think we have a good grasp of those trade-offs here and have proper solutions to mitigate them.
Before jumping into details though, it is important to point out that - depending on the use case - parameters for concerns around each of those categories of issues change. For example, we also use Zoom in the RIPE NCC for our day-to-day work, but there, we have company provided laptops for staff with additional security and policy considerations, which makes it acceptable for us to use as the tool for our business (we reconsider that decision and the risk we are taking with the news of each vulnerability and are still using Zoom). But that can not be said about a RIPE Meeting. We want to be as inclusive as possible and we can not expect everyone to have the same setup to mitigate some of the risks. In this article, we will only focus on using Zoom for RIPE 80 and the RIPE NCC General Meeting (GM).
Meeting Security and privacy
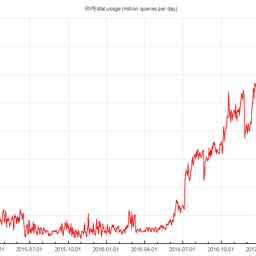
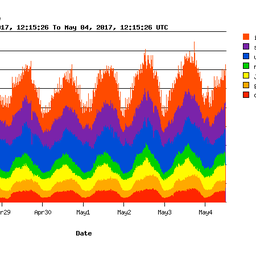
With the exponential growth Zoom experienced, not only public scrutiny was expected but also vandalism. So far, Zoom has been acceptably reactive to addressing issues pointed out by security researchers and the general public, but that’s certainly not enough. For most of RIPE 80 and the GM, we will use Zoom Webinar mode. Webinar mode allows clients to join the meeting as a normal meeting but depending on the choice of host, they can be either "panelists" or "attendees”. “Panelists” who would be the relevant chairs, presenters and support team members have all the tools that a normal zoom user has: they can start and stop their audio and video, share their screen (if allowed) and present. “Attendees” however, can only access the audio, video and presentation shared by panelists, and they can participate in chat and Q&A.
There will be clear guidance on the online etiquette for the RIPE 80 Meeting participation but there is a range of options: Meeting hosts can upgrade any user from “attendee” to “panelist” on the fly, and session chairs can read out the questions typed in chat or provide a combination of these. This approach will mitigate risks referred to as Zoom-bombing or other types of vandalism in the meeting. This also reduces the annoyance and risk of not having a muted microphone or sharing unwanted video or content just to the “panelists”. There are other concerns with meeting privacy though. Will zoom store a copy of content shared during the meeting? Although a serious question, this is not a real concern for the RIPE Meeting or the GM, as they are open meetings and all of the content is always streamed in real time and also published for future use.
User Security
There is a concerning number of technological decisions or oversights which undermines user security, when installing and using the Zoom app. Although they really depend on the platform used (i.e. Windows vs. Mac vs. Linux vs. phone OS, etc.). This is not the right space nor am I the type of expert to jump into the details of those, but I have enough grasp of Information Security to tell you that some of them were or are concerning. One would think how it is even possible to not consider those issues from the start? As said before, for us as an organisation, Zoom's response to concerns raised has been acceptable so far. They are addressing most of those issues and many have already been fixed. That said, based on the trend (except if you are confident of your level of security knowledge and control over your device), we recommend you to either use Zoom in the web browser, which addresses a good number of security dangers (well, it offloads most of it to your browser and that becomes your main security bottleneck, but it already is, isn’t it?) or even better, have a lightweight VM and run Zoom from within that VM. If you have a company laptop or other device and your organisation uses or allows use of Zoom under their security policy, then using that device is also an option.
Finally, if you prefer, or because of your company policies you have to distance yourself from Zoom, we are committing to our usual remote participation service as well. Although the meetings will be run inside Zoom rooms, we will stream the video on our own local infrastructure (over IPv6 and also legacy IPv4) as usual and will maintain our usual IRC chat channel for tunnelling questions to the room, to be read by the meeting chat monitor. In the end, the tooling is your choice. We have tried to be as inclusive as possible and keep the balance between being able to organise a professional event with proper security and accessibility.
User Privacy
Were you aware that Zoom has a feature to report to the meeting host if you have the zoom app in focus or not? What about the fact that the meeting host receives a log of all of the chats, including the “private” ones at the end of the meeting? Did you know that the hosts can unmute the microphone of panelists? We went through the full list of Zoom features and have disabled some by default (for example, by default anyone who joins meetings created by the RIPE NCC will join in the muted state). We will never unmute anyone, and we will never force joining meetings with camera. We will never use the attention-tracking feature. And we will always clearly inform attendees if the meeting is supposed to be recorded (which is standard for all RIPE Meetings). Also, we will inform users not to share sensitive information in private chats.
The RIPE NCC's internal policy for Zoom use is updated frequently according to changes with the Zoom platform, and it deals extensively with security, privacy and confidentiality issues. This policy is the basis for our Zoom usage internally and externally.
Finally, I have to say, it is not an easy decision to say we are using Zoom for RIPE 80, but in the absence of other viable options that provide the reliability, scale, support and legal and contractual requirements we have, we are confident this is the best choice especially when everything mentioned here is considered. Given the fact that all RIPE sessions are open and public by default, it makes this choices easier and eliminates some of the concerns, but this is still a complex issue with many dimensions. We know some users in our service region cannot access Zoom except if they use VPN, as Zoom (like all of other providers we have tested) doesn’t provide service to sanctioned countries. Providing our own live feed will mitigate that issue for those users.



Comments 8
The comments section is closed for articles published more than a year ago. If you'd like to inform us of any issues, please contact us.
Randy Bush •
As the NSA, PLA, Mossad, GCHQ, ASD, ... are not in my threat model, at least not for RIPE meetings, Zoom is a fine choice. The ease of use is important, and we have no secrets. Luckily, neither of my employers tells me how to run my laptops.
Jordi Palet Martinez •
Very informative. Thanks a lot! I love the "legacy IPv4" bit :--)
Juan Rodriguez •
You should consider using Jitsi Meet with an in-promises server.
Kurt Kayser •
Hi, My guess is this will be one of the toughest challenges for Zoom-Servers: load, parallel sessions (>1000?) . I hope this will withstand the RIPE crowd - although first time trials a rarely a huge success, but this time there no alternative. My suggestion: inform the Zoom-experts about our planned session and let them check, if things could get fixed fast during our week @RIPE80. It's a premiere, and no one to blame if it does not work out 100%, as we are usually hosted by the RIPE NCC meeting folx. Stay healthy, maintain social distance and hope to meet you in mid-May online through Zoom :-) Regards, Kurt
Colin Petrie •
Hi folks, While I understand with your reasoning of using Zoom, please enable the "Join from your browser" option so we are not forced to install their app. You can see how to check the settings here: https://support.zoom.us/hc/en-us/articles/115005666383-Show-a-Join-from-your-browser-Link Preferably, lock it so that it cannot be turned off. So far, I have been unable to join any of the DNS-WG Zoom sessions as I cannot use my browser to do so. Even though I regularly join Zoom chats with other organisations who do not restrict the use of the browser-based web client. I hope you can make this more inclusive for the community! Thank you!
Mirjam Kühne •
Thanks for bringing this up, Colin. In the article we suggest to users to use the web based client and it was definitely our intention to allow for that. We will see how we can enable that by default in time for the RIPE Meeting.
Colin Petrie •
Thanks Miriam, and everyone else!
Peter Gervai •
I am not really sure this would be the right place to provide a feedback on RIPE-80+Zoom, so I'll be unusually brief. It was a bad experience, after having been on Jitsi and BigBlueButton for months now. Just in few word points: Web UI was hard to access; Q&A window is an unfollowable mess (can't reply to private messages sent to me); the video source had to manually moved not to overlap something; chat window used up lot of space but turned out to be useless; video inserts has extreme sync loss; UI is a mess for various reasons. I have noticed that probably the "most useful" feature was the "AI greenboxing background", yeah, I'm kidding. Fortunately we had IRC to talk on. And, yes, obviously it's closed source, closed protocol, which is not really fine. Apart from all of these I see that it's easier to pay for a service and let the company resolve the problems, so I don't fight, until there's a web client running in a private window... I would not be happy if someone would force me to install an unreliable and security problem ridden application on my machine.