Legacy Out of Contract

I am a research engineer in the R&D department at RIPE NCC. I am interested in internet measurements, internet outages, data analysis, and cybersecurity. Prior to joining RIPE NCC, I defended my Ph.D. in cyber-security at Delft University of Technology (TU Delft), The Netherlands. More
• 19 min read
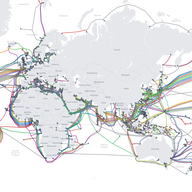
Last time, we looked at legacy address space in terms of contract coverage, ROA coverage, and proportion of announced prefixes. Now it’s time to take a closer look at those blocks still to be brought under contract and get a clearer picture of what kind of behaviour we see coming from them.