The RIPE NCC held online BGP Security training for Ukrainian telecom operators on 6 April. The training was delivered in English with translation into Ukrainian. In this article, we talk about the motivation for providing this particular kind of training and share the full recording.
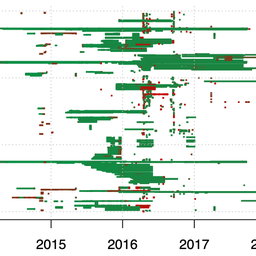
Since the war began, Ukrainian network operators have found themselves in a very difficult situation. Military actions continue to have a huge impact on Internet infrastructure in the country. Every day, equipment is being destroyed, fibre optic channels are being broken, and there are regular power outages. But communication services continue to be provided, and as Emile Aben showed in his article The Resilience of the Internet in Ukraine, the Ukrainian segment of the Internet is much more stable than one would expect under such conditions.
In order to help their Ukrainian colleagues, the RIPE NCC asked them what kind of consulting support they could most use right now. Most of the operators were in favour of online training on BGP Security. Some of them indicated that they themselves had been victims of BGP attacks since the war began, so this training could be of direct practical value.
We therefore decided to conduct BGP Security training for Ukrainian telecom operators online, with open participation - in other words, all operators were free to attend the training, not just RIPE NCC members. It took place on April 6, 2022. The training was accompanied by a translation into the Ukrainian language.
Note that , to our regret, there were some technical problems during the recording of the event, which meant that the Ukrainian audio track had to be restored (and partly recreated). While this caused a delay with this publication, we still very much hope that making this recording available now will be of use to the Internet community in Ukraine.
Ukrainian recording
English recording
After the war began, independent researchers also started paying attention to the importance of BGP security for Ukraine. On March 4, in his article Did Ukraine suffer a BGP hijack and how can networks protect themselves?, Aftab Siddiqui analysed available publications on violations of the routing system in the Ukrainian segment of the network, and provided statistics on measures already taken by Ukrainian operators. In general, it should be observed that, according to these statistics, not so many cases of BGP hijacks of Ukrainian prefixes have been detected yet. For example, BGPMon service from Cisco records only four such incidents. However, it is noteworthy that the incidents listed do not include those referred to in personal communication by Ukrainian telecom operators. This may indicate that some of these attacks, which can indeed be very complex, are going undetected.
More webinar recordings (in English) on this topic can be found here.
















Comments 0
The comments section is closed for articles published more than a year ago. If you'd like to inform us of any issues, please contact us.