Measuring Anycast DNS Services Using RIPE Atlas


Kenneth Finnegan
Based in San Jose, California, USA
Kenneth is one of the founders of the Fremont Cabal Internet Exchange, an exchange founded in the Silicon Valley to help promote peering participation from networks regardless of their budget. His day job is as an electrical engineer at Lam Research designing semiconductor fabrication equipment. More
• 12 min read
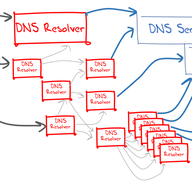
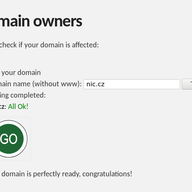
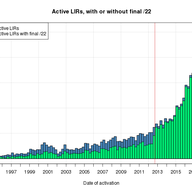
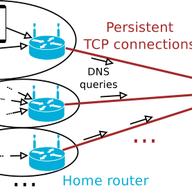
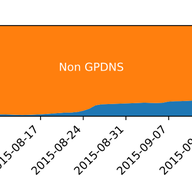
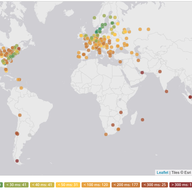
A step-by-step guide to how to use the RIPE Atlas measurements infrastructure to characterize the world-wide performance of Anycast DNS services.