How Cloud Edge Infrastructure Improves Round-Trip Time

I'm a master's student in Computer Science at the University of Crete. My research focuses on Internet measurements, with an emphasis on BGP, Internet topology, and network latencies. More
• 10 min read
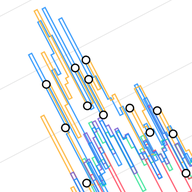
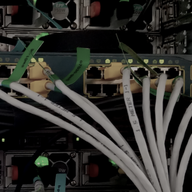
In this work, we investigate the improvements in network latency across six European countries - Germany, Finland, Poland, Bulgaria, Greece, and Czechia - when leveraging cloud edge infrastructure. Using ping measurements from RIPE Atlas, we analyse the impact of cloud edge solutions provided by th…