Visualising DNS Issues with DNSMON


Massimo Candela
Based in Amsterdam
At the time of writing articles listed here, Massimo Candela was Senior Software Engineer with R&D at the RIPE NCC, working mainly on developing web applications that provide a visual and interactive representation of large amounts of network data. Tools he played a key role in developing are go-to resources … More
• 4 min read
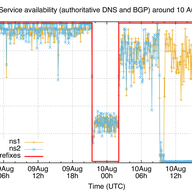
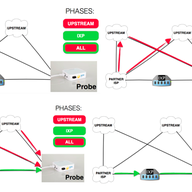
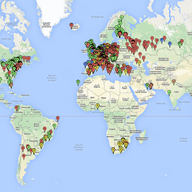
This article is a summary of an academic paper, Visualization and Monitoring for the Identification and Analysis of DNS Issues, that was presented at the Tenth International Conference on Internet Monitoring and Protection in Brussels in June 2015.