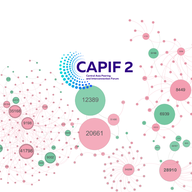
CAPIF 2: The Road to Interconnection


Anastasiya Pak
Based in Amsterdam
Anastasiya Pak is a Senior Marketing and Communications Officer at the RIPE NCC. Before joining the RIPE NCC, Anastasiya led the Communications Department at an international NGO and worked as a TV journalist in Uzbekistan, covering international politics, diplomacy, and global affairs. She holds a Bachelor's Degree in International Relations … More
• 11 min read
From 19-20 September, network operators, local IXPs, peering coordinators, Internet researchers and government officials will meet at CAPIF 2 to build a more diverse interconnection environment in Central Asia, Iran, and beyond. To prepare, we’ve been examining changes in local interconnection and …