Internet Protocols are Changing
Mark Nottingham
Based in Melbourne, Australia
I am a member of the Internet Architecture Board, and co-chair the IETF QUIC and HTTP Working Groups. More
• 12 min read
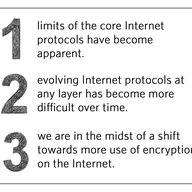
When the Internet started to become widely used in the 1990s, most traffic used just a few protocols: IPv4 routed packets, TCP turned those packets into connections, SSL (later TLS) encrypted those connections, DNS named hosts to connect to, and HTTP was often the application protocol using it all.